Thu 16 April 2026
Mobile is now the primary digital channel through which customers interact with financial institutions. Modern banking applications allow users to check account balances, transfer funds, pay bills, manage beneficiaries, and complete identity-related actions directly from their mobile devices. As these applications become more central to the customer experience, they also become more critical to the institution’s overall security posture.
Because mobile banking apps process highly sensitive financial and personal information, they are attractive targets for cybercriminals. Attackers may attempt to steal authentication credentials, intercept communications, abuse weak APIs, or manipulate transaction workflows for financial gain. The risk is amplified by the nature of mobile environments: banking apps run on devices that institutions do not control, communicate with multiple backend services, and depend on complex authentication, session, and payment logic. This combination creates a wide and dynamic attack surface.
Given this complexity, financial institutions need modern mobile security testing approaches that can assess how banking applications behave across the device, the network, and backend systems. This helps teams identify weaknesses earlier, validate whether sensitive data and critical workflows are properly protected, and give engineering teams clearer direction for remediation.
Why Mobile Banking Security Testing Matters
Mobile Application Security Testing, or MAST, is used to evaluate the resilience of mobile banking applications by identifying vulnerabilities before they can be exploited in real-world attacks. Effective mobile security testing combines static analysis, dynamic assessment, and runtime observation to examine application code, execution behavior, local storage, and network communication. Rather than producing only theoretical findings, modern mobile security testing can also generate technical evidence such as logs, traces, and execution artifacts that help engineering teams verify issues and prioritize remediation with confidence.
Mobile financial applications handle some of the most sensitive information in the digital ecosystem. This includes personal identity data, authentication secrets, account records, and transaction details. Any weakness affecting this environment can have direct financial consequences as well as serious reputational and regulatory impact.
Several factors make mobile banking security especially complex. Financial applications process high-value and highly sensitive data, which naturally attracts cybercriminals. They also run across diverse hardware and operating systems such as iOS, Android, and in some contexts HarmonyOS, which increases the number of technical variables security teams must consider. At the same time, users may access these applications from untrusted or compromised devices, creating additional exposure that institutions cannot fully control.
Compared with traditional web applications, mobile apps also introduce additional security considerations. They rely on local storage, runtime execution environments, embedded components, app permissions, deep links, and mobile-specific frameworks. As a result, organizations need testing methods that go beyond standard web security practices and account for the specific realities of the mobile ecosystem.
Security testing helps financial institutions verify that protection mechanisms are functioning consistently across both frontend and backend systems. It allows teams to identify weaknesses in critical user journeys, validate whether sensitive data is handled securely, and confirm that security controls remain effective as the application evolves through frequent releases and updates. The scale of existing weaknesses shows why this matters: hardcoded secrets affected over 50% of apps in the study, while outdated libraries were found in 46%.
For a deeper look at the data behind these findings, read the full Banking Report 2025, based on a large-scale study of 500+ mobile banking apps
The Mobile Banking Attack Surface
Effective security requires institutions to look at mobile banking as a full ecosystem rather than a standalone app. A typical banking environment spans the client device, the network communication layer, and backend systems. Each layer introduces a different type of risk, and attackers often move across these layers rather than targeting just one of them.
At the client level, the main assets at risk include user credentials, app logic, and locally processed data. On the network side, the primary concern is data in transit, including authentication tokens, account details, and transaction information. In backend systems, the highest-value assets include identity management services, financial records, and transaction processing logic. Protecting mobile banking apps therefore requires coordinated security controls across all three layers.
| Layer | Primary Asset at Risk | Common Mitigation |
|---|---|---|
| Client | User Credentials & App Logic | Obfuscation & Root Detection |
| Network | Data in Transit | Certificate Pinning & Encryption |
| Backend | Personal & Financial Data | Robust IAM & API Gateways |
Device-Level Risks
The user device is often the first point of attack in mobile banking threats. Attackers may try to reverse engineer application binaries to understand how the app works, identify hidden functionality, or extract hardcoded secrets. On compromised devices, they may also attempt malware injection or runtime manipulation in order to bypass security controls or change how the app behaves during execution. Since financial institutions cannot fully control the health or trust level of a user’s phone, application-level protections such as obfuscation, runtime checks, and hardening techniques are especially important. This matters even more in a market where older application foundations remain common: in a large-scale study of 500+ mobile banking apps,25% of iOS apps analyzed were released between 2008 and 2011, another 22% between 2011 and 2014, and 27% of Android apps between 2010 and 2013.
Network Communication Risks
Mobile banking applications rely heavily on communication with backend APIs for authentication, account access, and payment flows. If this communication is not properly secured, attackers may attempt man-in-the-middle attacks to intercept or modify traffic. This can expose authentication tokens, session data, or transaction details in transit. Strong transport security, certificate validation, and secure session handling are essential to reduce this risk. The continued presence of weak transport practices reinforces this point, with cleartext HTTP still found in 20% of the analyzed banking apps.
Backend System Risks
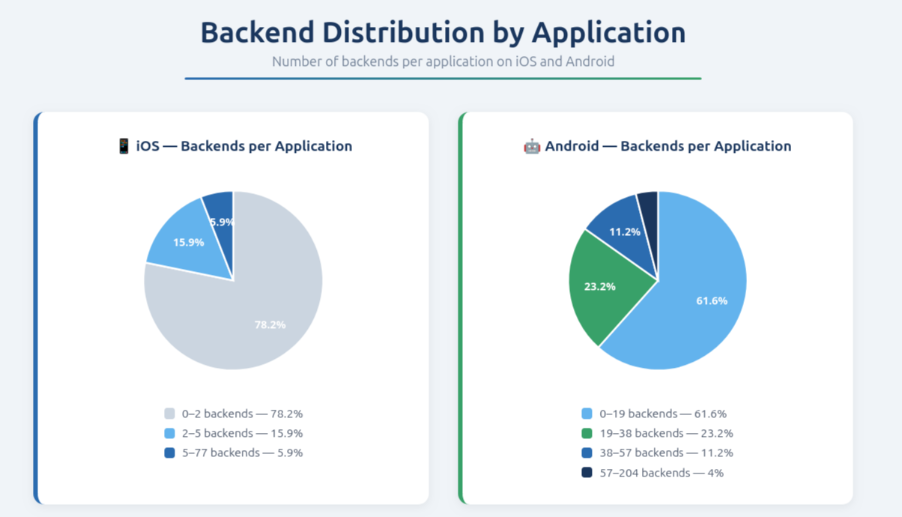
Even if the mobile client itself is well protected, weaknesses in backend authentication, authorization, or transaction validation can still lead to fraud or data leakage. Attackers may exploit poorly secured endpoints, weak identity flows, or missing authorization checks to gain access to sensitive records or perform unauthorized actions. In practice, mobile banking security is only as strong as the backend systems supporting the app. Backend concentration also increases systemic exposure: 78% of iOS banking apps in the study connected to two or fewer backends, and over 77% of banking app backends were US-based.
This concentration is also visible at the infrastructure level. Ostorlab’s Banking Report 2025 shows that many mobile banking apps rely on a limited number of backend systems, which increases the importance of securing APIs, identity services, and transaction validation layers.
Critical Mobile Banking Workflows That Require Strong Protection
Mobile banking applications rely on a small number of workflows that carry especially high risk. If these workflows are compromised, attackers may gain unauthorized access to accounts, redirect transactions, or expose sensitive financial data. These areas should therefore be treated as security priorities during testing.
Authentication and Identity Verification
Authentication is one of the most critical functions in a banking application because it controls access to the entire user environment. Mobile banking apps commonly rely on a mix of passwords, biometrics, one-time codes, and token-based systems. Security testing in this area examines whether authentication logic can be bypassed, whether session tokens are predictable or improperly protected, whether biometric verification is securely implemented, and whether login flows can be manipulated. Since authentication is the gateway to all sensitive operations, even small weaknesses can have major consequences. This is especially relevant because biometric authentication now appears in 65% of banking apps, yet biometric bypass vulnerabilities were still observed in 28% of them.
Session Management Security
Session handling determines how a user’s identity is maintained during application usage and how access is ended when a session expires or the user logs out. Weak session management can allow attackers to hijack active sessions, reuse expired credentials, or keep access longer than intended. Testing should therefore evaluate token lifecycle controls, logout behavior, expiration logic, token storage, and whether session fixation or reuse is possible under abnormal conditions.
Payment and Transfer Workflow Protection
Payments and transfers are among the most sensitive actions in any banking application because they involve direct movement of funds. Security testing should verify that transaction requests cannot be modified through client-side manipulation, that payment amounts and destination details are validated correctly, and that backend authorization checks are consistently enforced. Unauthorized transaction modification remains one of the most important fraud scenarios in mobile banking, so this workflow requires strong client and server-side protections.
Beneficiary Management Security
Beneficiary management is another high-risk area because many fraud schemes involve attempts to add unauthorized recipients or modify payment details. If attackers can alter beneficiary records or redirect payments to malicious accounts, the impact can be immediate and severe. Strong server-side validation, approval flows, and monitoring are essential to protect these features. Because beneficiary management is closely tied to fraud risk, it should be continuously assessed as part of mobile security testing.
Common Vulnerabilities in Mobile Banking Applications
Mobile banking apps may contain weaknesses across multiple technical layers, and these vulnerabilities can affect both the application itself and the wider financial environment around it. Understanding these categories helps teams focus testing efforts where risk is highest.
Sensitive Data Exposure
Sensitive information such as authentication tokens, personal identifiers, and cryptographic material should never be stored in insecure locations. In mobile apps, risk often appears when secrets are written to local databases, shared preferences, caches, logs, or screenshots. Insecure memory handling can also expose valuable data during runtime. Because financial applications process highly confidential user and transaction information, this type of weakness can lead directly to account compromise or data leakage. This is not a marginal issue: hardcoded secrets alone affected over 50% of the analyzed apps, exposing API keys, tokens, or credentials in code.
KYC Flow Security Risks
Customer identity verification processes are increasingly built directly into mobile applications. Document uploads, selfie verification, and identity capture steps create additional exposure because they involve highly sensitive personal data. If these workflows are poorly secured, identity verification artifacts may be stored persistently, cached insecurely, or left exposed through weak session state controls. Security testing should treat KYC processes not only as business functions, but also as critical data handling workflows.
Cryptographic Implementation Weaknesses
Encryption plays a central role in protecting banking applications, yet implementation mistakes remain common. Problems can appear when apps rely on outdated cryptographic algorithms, use hardcoded keys, or fail to manage key rotation and lifecycle properly. Weak cryptographic design can undermine the confidentiality of both stored and transmitted data, making it a major concern in financial environments where trust and integrity are essential.
Client-Side Security Control Weaknesses
Security decisions should not rely solely on client-side logic because mobile applications can be reverse engineered and manipulated. If important checks are enforced only in the app itself, attackers may bypass them by modifying runtime behavior, abusing hidden controls, or interacting directly with APIs outside the intended interface. Strong security design requires critical decisions to be validated on the server side rather than trusted to the client alone.
Application Tampering and Resilience
Attackers may attempt debugging abuse, runtime injection, code modification, or unauthorized instrumentation in order to understand or alter how the application behaves. For a banking app, this can weaken trust boundaries and make further abuse easier. Application hardening and resilience techniques help preserve integrity during execution and reduce the chance that attackers can manipulate the app successfully.
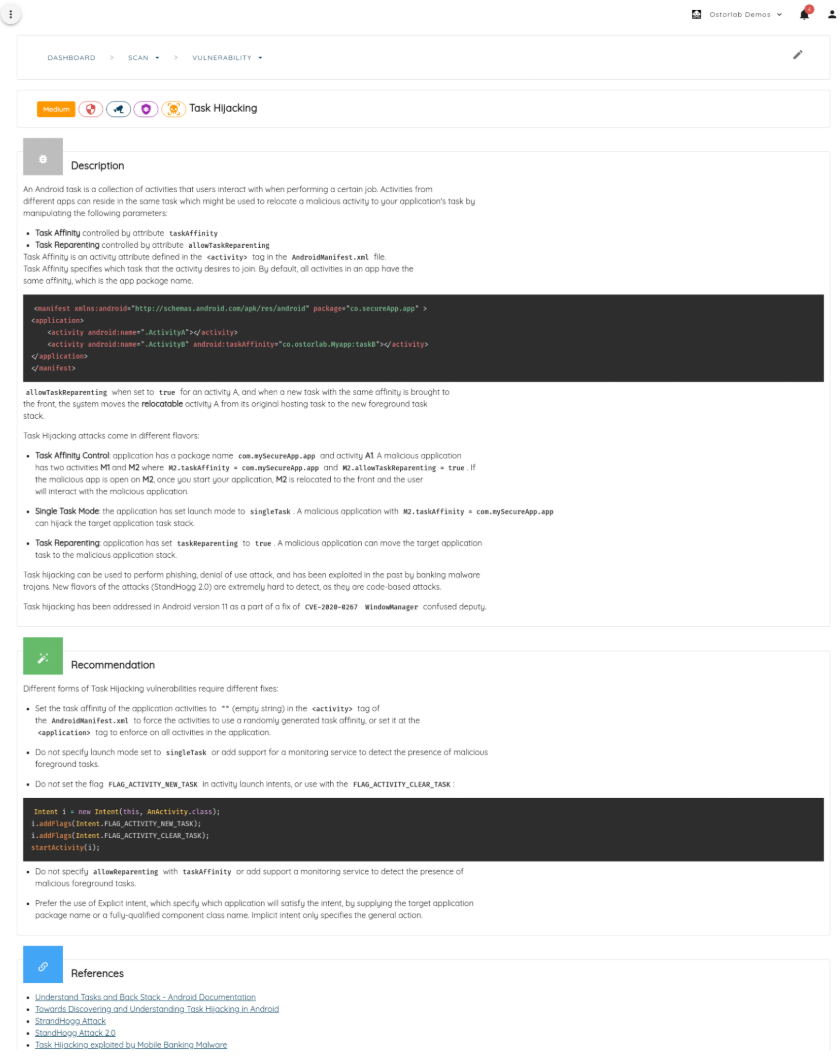
WebView and Deep Link Security Risks
Embedded browser components and navigation schemes can introduce vulnerabilities when they are not implemented carefully. Injection inside WebView contexts, malicious redirection through deep links, and session hijacking through URL manipulation can all create openings for unauthorized actions. These issues are especially important in mobile banking because even a small navigation flaw may expose authentication, session, or payment-related workflows.
Supply Chain and Third-Party Component Risks
Modern mobile banking applications depend on third-party SDKs, libraries, and embedded frameworks. While these components accelerate development, they also introduce risk when they are outdated, vulnerable, or compromised. Supply chain risk is becoming increasingly important in mobile security because vulnerabilities may originate not only in the bank’s own code, but also in external dependencies that the app relies on. The scale of the issue is clear in the research, where outdated libraries affected 46% of banking apps.
Evidence Generated by Mobile Security Testing
Effective security validation must provide more than a list of theoretical findings. It should generate evidence that helps teams understand what was found, why it matters, and how to fix it. This is particularly important in banking environments, where security decisions often need to be reviewed by both engineering and compliance stakeholders.
- Decompiled Application Context
- File System Activity Evidence
- Code Path Execution Coverage
- Triage-Ready Investigation Artifacts
Regulatory and Compliance Considerations
Financial institutions must align their mobile banking security programs with industry regulations and cybersecurity frameworks. Because mobile applications handle sensitive customer data and support critical transactions, regulators increasingly expect institutions to demonstrate strong controls, resilient systems, and continuous testing practices.
Security testing supports these expectations by helping organizations verify that safeguards are implemented correctly and functioning as intended. It also helps security teams build stronger internal assurance around data protection, payment security, and operational resilience.
NIS2
NIS2 introduces cybersecurity and risk management obligations for essential sectors, including parts of the financial ecosystem. For mobile banking, this reinforces the need for visibility into application risk and stronger resilience practices.
DORA
DORA focuses on operational resilience and ICT risk management for financial institutions. In the mobile banking context, this highlights the importance of testing critical digital services and validating that security controls remain effective over time.
PCI DSS
PCI DSS defines standards for protecting payment-related data. Any mobile application involved in payment processing must align with these requirements to help protect cardholder data and secure transaction flows.
FFIEC guidance
FFIEC guidance outlines cybersecurity testing and audit expectations in the financial sector. For mobile applications, this strengthens the case for repeatable security validation and clear evidence that risk is being monitored and addressed.
GLBA
GLBA requires institutions to safeguard consumer financial information. Since mobile banking apps often process and store this data in various forms, strong testing and protection measures are essential to support compliance.
OWASP Mobile Top 10
The OWASP Mobile Top 10 remains a useful reference for understanding common categories of mobile risk. It can help teams structure testing efforts and communicate technical risks in a more standardized way.
Integrating Mobile Banking Security Testing into the Development Lifecycle
A modern mobile security strategy should not depend only on occasional post-development assessment. Because banking applications evolve quickly, security testing needs to be embedded into the development lifecycle so that issues can be identified earlier and reassessed after changes.
CI/CD Integration
Integrating security scanning into CI/CD pipelines helps teams detect issues earlier in the release process and maintain more consistent testing coverage as the application evolves. This supports faster feedback and reduces the cost of late-stage remediation.
Issue Tracking and Remediation Workflows
Security findings should connect naturally to issue tracking systems so engineering teams can review, prioritize, and resolve them in an organized way. This improves collaboration between security and development and helps ensure that vulnerabilities are not lost between assessment and remediation.
Identity and Access Controls
Access to testing platforms, findings, and remediation data should be controlled carefully, especially in financial environments. Strong identity and access management around security workflows helps protect sensitive information and maintain accountability.
Continuous Reassessment
Even small application updates, dependency changes, or backend modifications can introduce new weaknesses. Continuous reassessment helps ensure that security controls remain effective over time rather than being treated as one-time checks.
Mobile banking applications sit at the center of modern financial services, but their importance also makes them prime targets for attackers. Protecting these platforms is not a one-time project. It requires continuous testing, stronger resilience across devices, networks, and backend systems, and technical evidence that helps teams validate and fix issues efficiently.
By embedding proactive mobile security testing into the development lifecycle, financial institutions can identify vulnerabilities before they are exploited, strengthen the protection of high-risk workflows, and better support regulatory expectations. In an increasingly mobile-first financial environment, this level of diligence is no longer optional. It is essential for reducing risk, maintaining customer trust, and delivering a more secure digital banking experience.
Table of Contents
- Why Mobile Banking Security Testing Matters
- The Mobile Banking Attack Surface
- Critical Mobile Banking Workflows That Require Strong Protection
- Common Vulnerabilities in Mobile Banking Applications
- Evidence Generated by Mobile Security Testing
- Regulatory and Compliance Considerations
- Integrating Mobile Banking Security Testing into the Development Lifecycle