Fri 27 February 2026
Mobile pentesting has evolved from basic manual testing to include automated scanning, AI-assisted analysis, and advanced reverse engineering. Today’s tools help security teams handle complex apps and uncover hidden vulnerabilities efficiently. This list highlights the top 10 mobile app pentest tools our security team uses in real-world testing.
Mobile App Pentest tools at a Glance
All of the tools listed below are free and open-source, each serving a specific role in mobile penetration testing. This table provides a quick overview of the platforms they support, their primary purpose, and typical use cases.
| Category | Tool | Platform | Primary Purpose / Use Case |
|---|---|---|---|
| Dynamic Runtime Analysis | Frida | Android & iOS | Runtime instrumentation, hooking, bypassing security controls, inspecting cryptography and authentication flows. |
| Static Analysis and Reverse Engineering | Ghidra | Android & iOS | Low-level binary analysis, firmware and library reverse engineering, malware analysis. |
| JADX | Android | Android APK decompilation to Java-like source code, static inspection, obfuscated code review. | |
| Network Traffic Analysis | mitmproxy | Android & iOS | Interactive HTTP/S/WebSocket interception and manipulation for API testing and security validation. |
| Wireshark | Android & iOS | Packet-level network capture and inspection, protocol debugging, data leak discovery. | |
| Automation and Orchestration | OXO | Android & iOS | Coordinating multiple mobile security tools, workflow automation, scalable testing pipelines. |
| Python | Android & iOS | Custom scripting, automation, glue between tools, exploit prototyping. | |
| AI-Assisted Development | OpenCode / Claude Code / Gemini Code | Android & iOS | Accelerates code writing, scripting, exploit prototyping, and testing automation. |
| Infrastructure / Lab Setup | Docker / Docker Compose | Android & iOS | Reproducible, isolated testing environments for tools and backend services. |
| Automated Vulnerability Scanning | Nuclei | Android & iOS | Template-driven, fast, and scalable scanning for CVEs, misconfigurations, and exposed endpoints. |
1. Frida
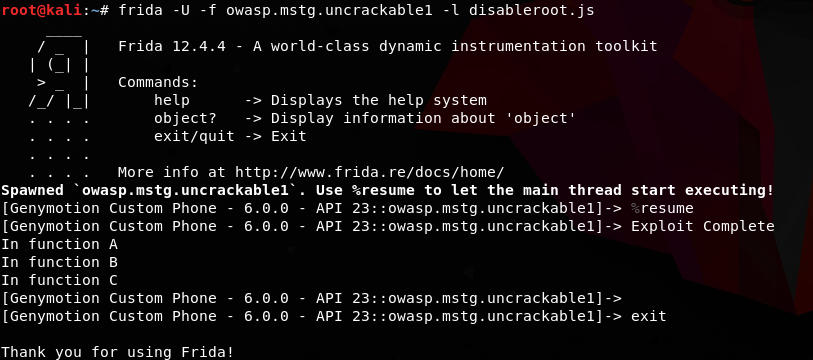
Frida enables deep runtime analysis and instrumentation of mobile applications. Instead of reversing, modifying, recompiling, and reinstalling apps, our security team uses Frida to attach directly to a live process, inject custom scripts, and observe behavior instantly.
In real-world mobile pentests, we use Frida to trace internal logic, hook cryptographic and authentication flows, bypass security controls, and dynamically analyze runtime behavior, making it one of the fastest and most powerful tools for advanced mobile security testing.
What It’s Best Used For
- Primary focus: Runtime manipulation and dynamic analysis of mobile applications.
- Core application: Hooking and inspecting cryptographic and authentication logic.
- Operational purpose: Observing and modifying application behavior in real time.
- Testing objective: Security control bypass testing without modifying binaries.
Where It Excels
- Live hooking: Intercepting and modifying app behavior at runtime without requiring source code or recompilation.
- Function and API hooking: Observing, modifying, and bypassing security-critical logic such as authentication checks, encryption routines, and API request handling.
- Real-time scripting: Injecting scripts into running processes and observing changes instantly.
- Cross-platform coverage: Android, iOS, Windows, macOS, Linux, watchOS, tvOS, FreeBSD, and QNX.
- Multi-language support: Python, Node.js, Swift, .NET, Go, and C.
- Open source: Free for security testing and research.
Limitations & Trade-offs
- Steep learning curve: Requiring understanding of operating system internals, application runtimes, and scripting.
- No built-in vulnerability scanning: Manual detection, reporting, and workflow implementation required.
- Manual effort required: Custom scripting needed per application.
- Detection by hardened applications: Runtime integrity checks and anti-hooking protections.
- Operational complexity: Setup challenges on rooted Android and jailbroken iOS devices.
Typical Use Cases in Our Assessments
- SSL pinning bypass: Bypassing certificate validation and network security controls.
- Authorization testing: Runtime testing of access control and privilege enforcement.
- Cryptographic inspection: Hooking crypto APIs to inspect encryption logic and key handling.
- Anti-tampering bypass: Defeating anti-debugging and runtime protection mechanisms.
- Logic tracing: Tracing sensitive application logic during authentication and session handling.
2. Ghidra
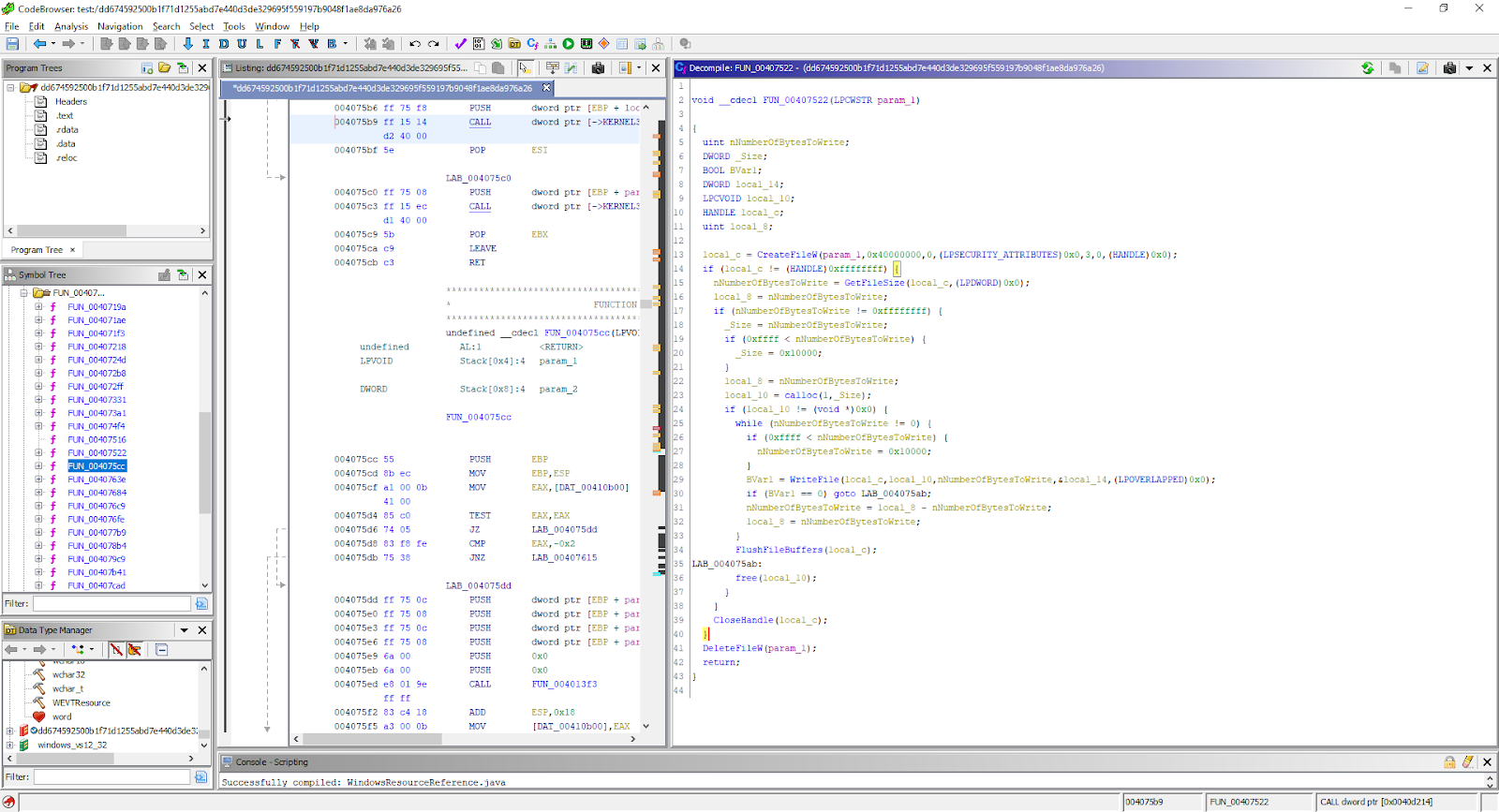
Ghidra is an open‑source software reverse engineering framework developed and maintained by the United States National Security Agency (NSA) to support deep binary analysis and vulnerability research. Originally built as an internal tool to help NSA analysts understand complex compiled code, automate large‑scale reverse engineering workflows, and collaborate on security projects, Ghidra was publicly released in 2019 with the full source code published on the NSA’s official GitHub repository.
Our security team uses Ghidra when we need to analyze compiled mobile binaries, firmware, and libraries without source code access, enabling us to unravel application logic, identify hidden behaviors, and discover vulnerabilities that dynamic or abstraction-focused tools often cannot detect, because they don’t analyze the program at the low-level binary level like Ghidra does.
What It’s Best Used For
- Primary focus: Static analysis of compiled binaries, especially for security research and vulnerability identification.
- Core application: Reverse engineering mobile binaries, embedded firmware, and third‑party libraries.
- Operational purpose: Understanding deep internal logic of software when source code is unavailable.
- Testing objective: Malware analysis, vulnerability discovery, and detailed control and data flow inspection.
Where It Excels
- Disassembly and decompilation: Translates machine code into assembly and high‑level C‑like pseudocode, helping our team interpret complex logic quickly.
- Multi‑platform architecture support: Handles binaries for many architectures (x86, ARM, MIPS, PowerPC, etc.), making it ideal for mobile, IoT, and embedded analysis.
- Graphical code navigation: Visualizes control flow graphs, call trees, and function relationships to make it easier to dissect complicated code paths.
- Scripting and automation: Supports Java and Python to automate repetitive tasks and integrate custom analysis routines into our workflows.
- Modular and extensible: Plugin architecture allows customization and extension for specialized tasks.
- Collaboration features: Allows multiple analysts to work on the same project, track changes, and share findings efficiently.
- Open source: Freely available under an open‑source license, encouraging community contributions and rapid evolution.
Limitations & Trade‑offs
- Static analysis only: It does not perform live runtime tracing or hooking, so dynamic behaviors must be investigated with other tools.
- Steep learning curve: Effective use requires strong understanding of assembly, binary formats, and reverse engineering concepts.
- Obfuscated code complexity: Heavily optimized or obfuscated binaries can require significant manual effort.
- Performance overhead: Very large binaries or projects can be resource‑intensive to analyze.
- Setup and configuration: Initial setup and project configuration can take time to optimize for team workflows.
Typical Use Cases in Our Assessments
-
Reverse engineering native libraries: Analyzing compiled ARM binaries inside Android and iOS applications to understand security-critical logic and uncover hidden vulnerabilities.
-
Malware and trojan analysis: Investigating suspicious or malicious mobile binaries to identify backdoors, command-and-control behavior, and data exfiltration mechanisms.
-
Third-party SDK auditing: Inspecting proprietary SDKs and closed-source libraries integrated into mobile apps to assess their security posture and trust assumptions.
-
Firmware and embedded component analysis: Reverse engineering embedded components and firmware that interact with mobile applications or backend systems.
-
Vulnerability research: Discovering memory corruption issues, unsafe logic flows, cryptographic weaknesses, and insecure implementations inside native code.
-
Protocol and algorithm reconstruction: Rebuilding undocumented protocols, cryptographic schemes, and proprietary algorithms used by mobile apps and their backends.
3. Jadx
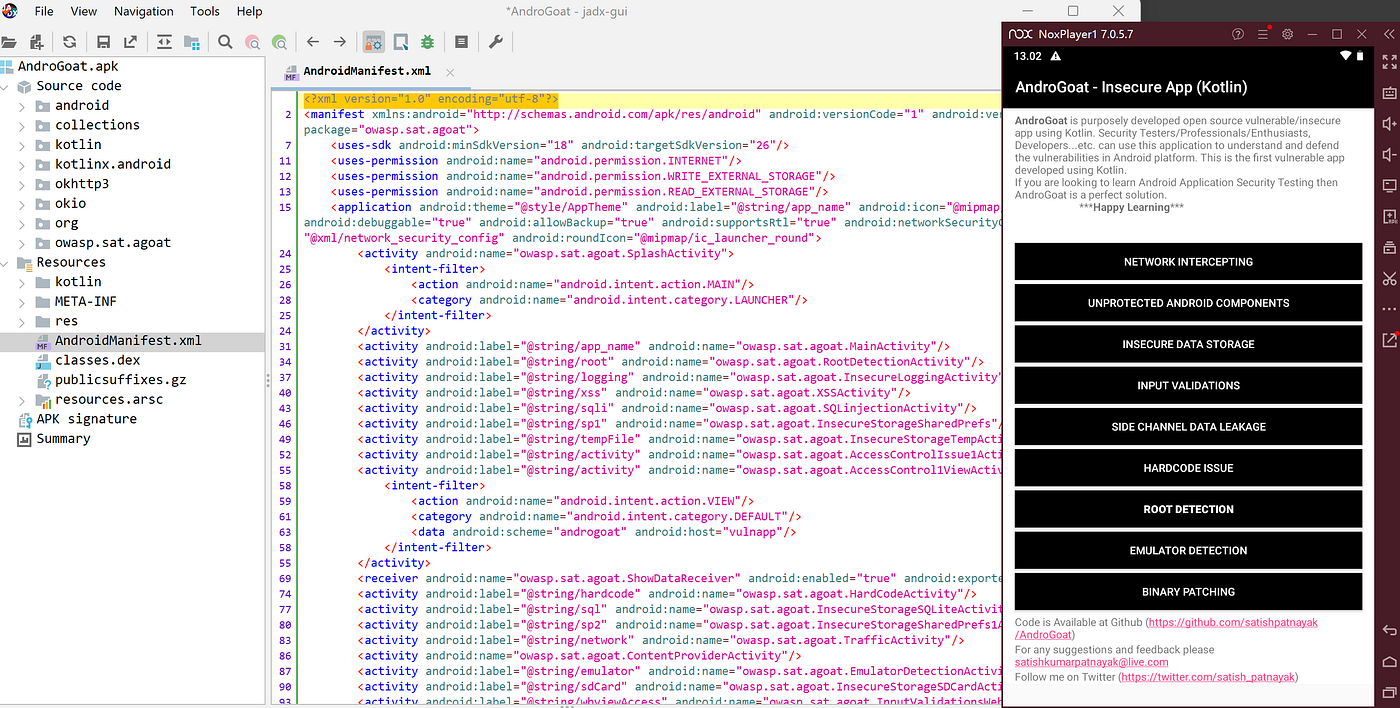
JADX is an open‑source Android decompiler that allows our security team to convert DEX bytecode inside APKs into human-readable Java source code, making it much easier to analyze mobile applications without access to the original source. We use JADX during mobile pentests to trace function calls, inspect API and cryptographic routines, understand application architecture, and identify potential vulnerabilities that would be difficult to spot by just reading smali or raw bytecode.
What It’s Best Used For
- Static analysis of Android applications: Recovering Java-like source code from APKs and DEX files for easier inspection.
- Reverse engineering third-party libraries and firmware: Understanding logic when source code isn’t available.
- Malware and security research: Examining app behavior, authentication routines, and sensitive data handling.
- Obfuscated code inspection: Improving readability of obfuscated Android applications to locate potential security flaws.
- Integration into custom workflows: Using the CLI or library mode to automate decompilation in pipelines or tooling.
Where It Excels
- Java-like output: Converts Dalvik/ART bytecode into structured, readable Java code, simplifying analysis.
- Multi-format support: Handles APKs, DEX, JAR, class files, AAR libraries, and Android App Bundles (AAB).
- Interactive GUI: Allows browsing decompiled classes, resources, and manifests, with syntax highlighting and navigation.
- Command-line interface: Enables batch processing and automation in security workflows.
- Deobfuscation support: Helps improve readability for apps protected with basic obfuscation techniques.
- Open source: Freely available and actively maintained by the community, allowing integration and customization.
- Lightweight and fast: Efficient decompilation for most Android applications without heavy resource requirements.
Limitations & Trade‑offs
- Imperfect decompilation: Decompiled Java code may be incomplete or require manual interpretation, especially in complex or optimized code.
- Obfuscation challenges: Heavily obfuscated apps may remain difficult to analyze even with deobfuscation tools.
- Static analysis only: Does not perform runtime tracing or hook into live application behavior.
- Limited support for some newer Android features: Certain bytecode patterns or optimized builds may generate less readable output.
- Learning curve: Effective use requires familiarity with Android app architecture, Java, and reverse engineering principles.
Typical Use Cases in Our Assessments
- Function and API tracing: Inspecting authentication, encryption, and network routines.
- Reverse engineering third-party SDKs and libraries: Understanding how external code interacts with the app.
- Malware and rogue app analysis: Examining code for hidden or malicious behavior.
- Obfuscated application review: Identifying security flaws in apps that use code obfuscation techniques.
- Integration with security tooling: Automating decompilation for batch analysis in CI/CD or internal pipelines.
4. mitmproxy
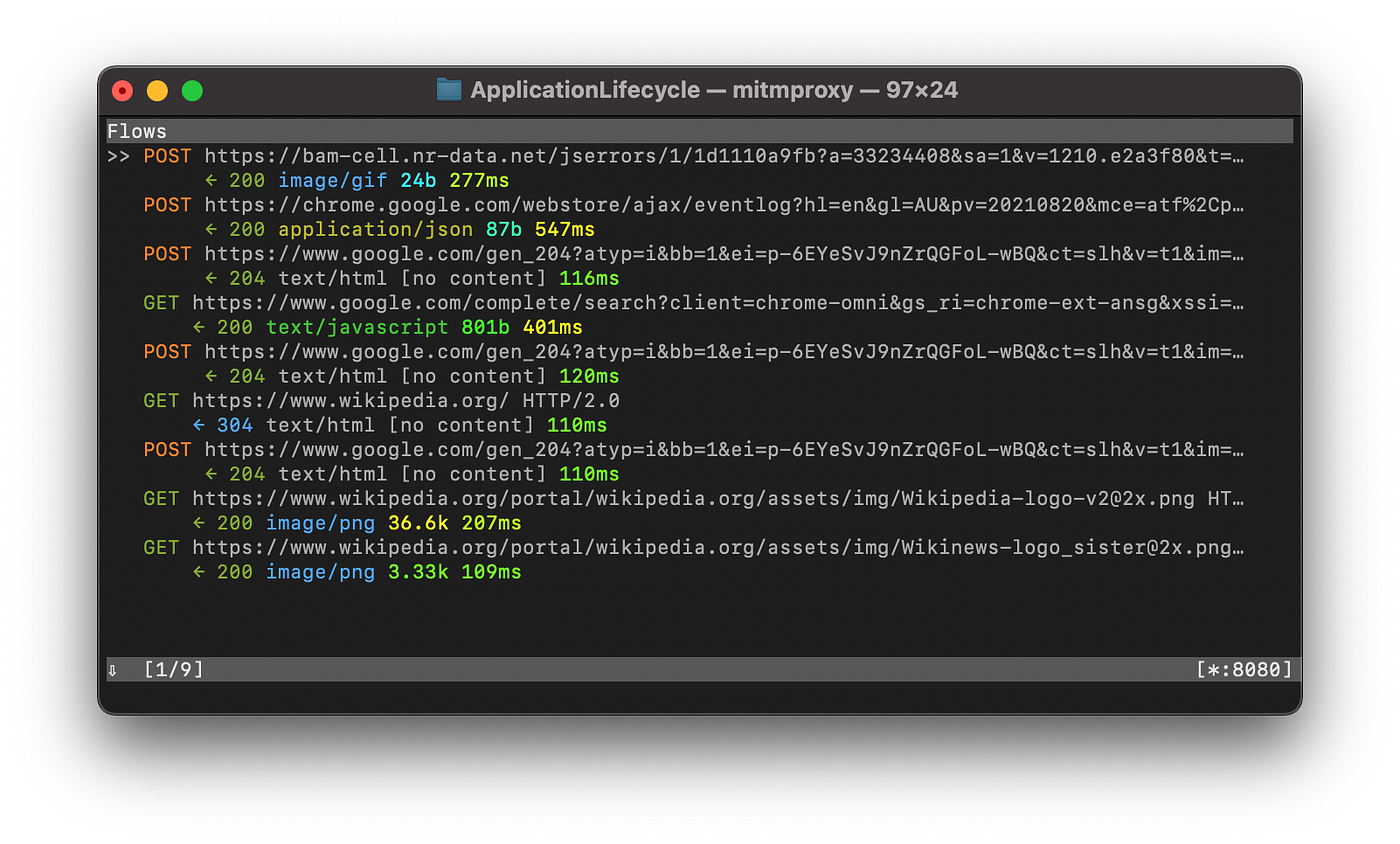
mitmproxy is an open‑source, interactive intercepting proxy that allows our security team to inspect, modify, and replay HTTP, HTTPS, and WebSocket traffic between mobile applications and backend servers. It acts as a man‑in‑the‑middle, decrypting encrypted communications in real time, which enables us to analyze API calls, manipulate requests, test authentication and session handling, and uncover hidden vulnerabilities that would otherwise be difficult to detect with standard network or debugging tools.
What It’s Best Used For
- Traffic inspection and debugging: Capturing, inspecting, and modifying HTTP/HTTPS requests and responses in real time.
- API request manipulation: Testing backend logic by altering parameters, headers, and payloads.
- Authentication and session testing: Validating token handling, session lifecycles, and authorization enforcement.
- Business logic testing: Detecting workflow flaws, logic bypasses, and improper trust assumptions.
- TLS and certificate analysis: Assessing transport security, encryption implementation, and certificate handling.
Where It Excels
- Real-time interception: Allows live inspection and editing of network traffic between mobile apps and servers.
- TLS decryption: Dynamically generates trusted certificates to decrypt encrypted communications for analysis.
- Interactive flow control: Pause, replay, or modify requests and responses on the fly to test backend behavior.
- Automation and scripting: Supports Python-based scripts to automate traffic manipulation, logging, and fuzzing.
- Flexible proxy modes: Works as a regular proxy, transparent proxy, reverse proxy, SOCKS proxy, or VPN-based interception.
- Modern protocol support: Handles HTTP/1, HTTP/2, HTTP/3, and WebSocket protocols used by mobile apps and APIs.
- Open source: Free and community-supported, allowing integration into internal workflows and custom tooling.
Limitations & Trade‑offs
- API traffic interception and manipulation: Capturing and editing requests/responses to evaluate backend logic.
- Authentication and session management testing: Testing login flows, token handling, refresh logic, and session invalidation.
- Broken access control and IDOR testing: Manipulating parameters to verify authorization enforcement.
- Business logic abuse testing: Identifying workflow bypasses, race conditions, and logic flaws.
- Backend injection vulnerability discovery: Detecting SQL injection, command injection, and deserialization flaws.
- TLS and certificate validation: Assessing encryption, certificate handling, and transport security controls.
Typical Use Cases in Our Assessments
-
API traffic interception and manipulation: Capturing and editing requests/responses to evaluate backend logic.
-
Authentication and session management testing: Testing login flows, token handling, refresh logic, and session invalidation.
-
Broken access control and IDOR testing: Manipulating parameters to verify authorization enforcement.
-
Business logic abuse testing: Identifying workflow bypasses, race conditions, and logic flaws.
-
Backend injection vulnerability discovery: Detecting SQL injection, command injection, and deserialization flaws.
-
TLS and certificate validation: Assessing encryption, certificate handling, and transport security controls.
5. Wireshark
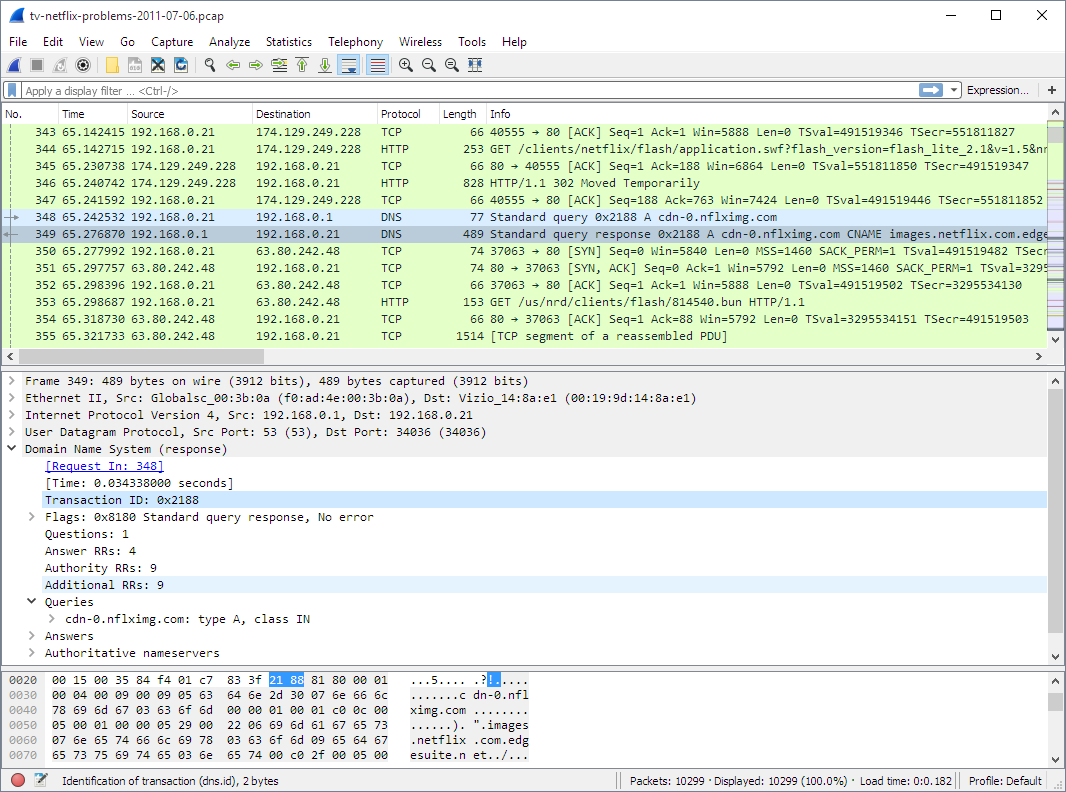
Wireshark is a free, open‑source network packet analyzer that allows our security team to capture, inspect, and decode raw network traffic at the packet level. It supports deep protocol dissection, real‑time capture, and detailed filtering and is widely used by security professionals for traffic analysis, anomaly detection, and troubleshooting across networks and applications.
In mobile application pentests, we use Wireshark to observe underlying network behavior, verify what traffic apps generate, detect cleartext leaks, debug protocol flows, and confirm how wireless or backend services communicate with clients. It gives us visibility into how packets move through the network, which is especially useful when diagnosing complex network interactions that happen outside of higher‑level proxies or application logs.
What It’s Best Used For
- Primary focus: Capturing and analyzing network packets at the lowest level.
- Core application: Inspecting traffic generated by mobile apps, backend services, and network hosts.
- Operational purpose: Correlating raw packet data with application behavior and network flows.
- Testing objective: Identifying suspicious traffic, protocol misuse, data leaks, and hidden communication channels.
Where It Excels
- Packet‑level visibility: Captures every frame on an interface and shows detailed breakdowns of protocol fields.
- Deep protocol dissection: Understands hundreds of protocols and decodes them into human‑readable fields.
- Real‑time and offline analysis: Can live‑capture traffic or analyze stored PCAP files.
- Powerful filtering: Advanced capture and display filters let us isolate specific conversations, endpoints, or protocols.
- Cross‑platform: Works across Windows, Linux, macOS, and other Unix‑like systems.
- TShark support: Command‑line equivalent for scripting and automation.
- GPL open‑source: Actively maintained with broad community support and extensibility.
Limitations & Trade‑offs
- Encryption challenges: It cannot decode encrypted application traffic (e.g., HTTPS) without the appropriate keys or external decryption techniques.
- Passive analysis: Wireshark captures and inspects traffic, but does not intrinsically manipulate or replay it; other tools like mitmproxy are needed for active testing.
- Interface visibility constraints: On switched networks or wireless interfaces without proper capture setup, it may only see limited traffic.
- Resource intensity: Capturing and analyzing high‑volume traffic can consume significant CPU, memory, and disk space.
- Steep learning curve: Interpreting packet details requires networking knowledge and familiarity with protocols.
Typical Use Cases in Our Assessments
- Network traffic confirmation: Validating backend API requests and responses seen in proxies like Burp or mitmproxy.
- Protocol behavior analysis: Understanding how mobile apps communicate at the TCP/IP level.
- Data leak discovery: Detecting unintended cleartext traffic or sensitive data exposure.
- Wireless traffic inspection: Capturing and analyzing traffic from test devices on controlled networks.
- Correlation with runtime behavior: Matching network events with runtime traces or security events.
6.OXO
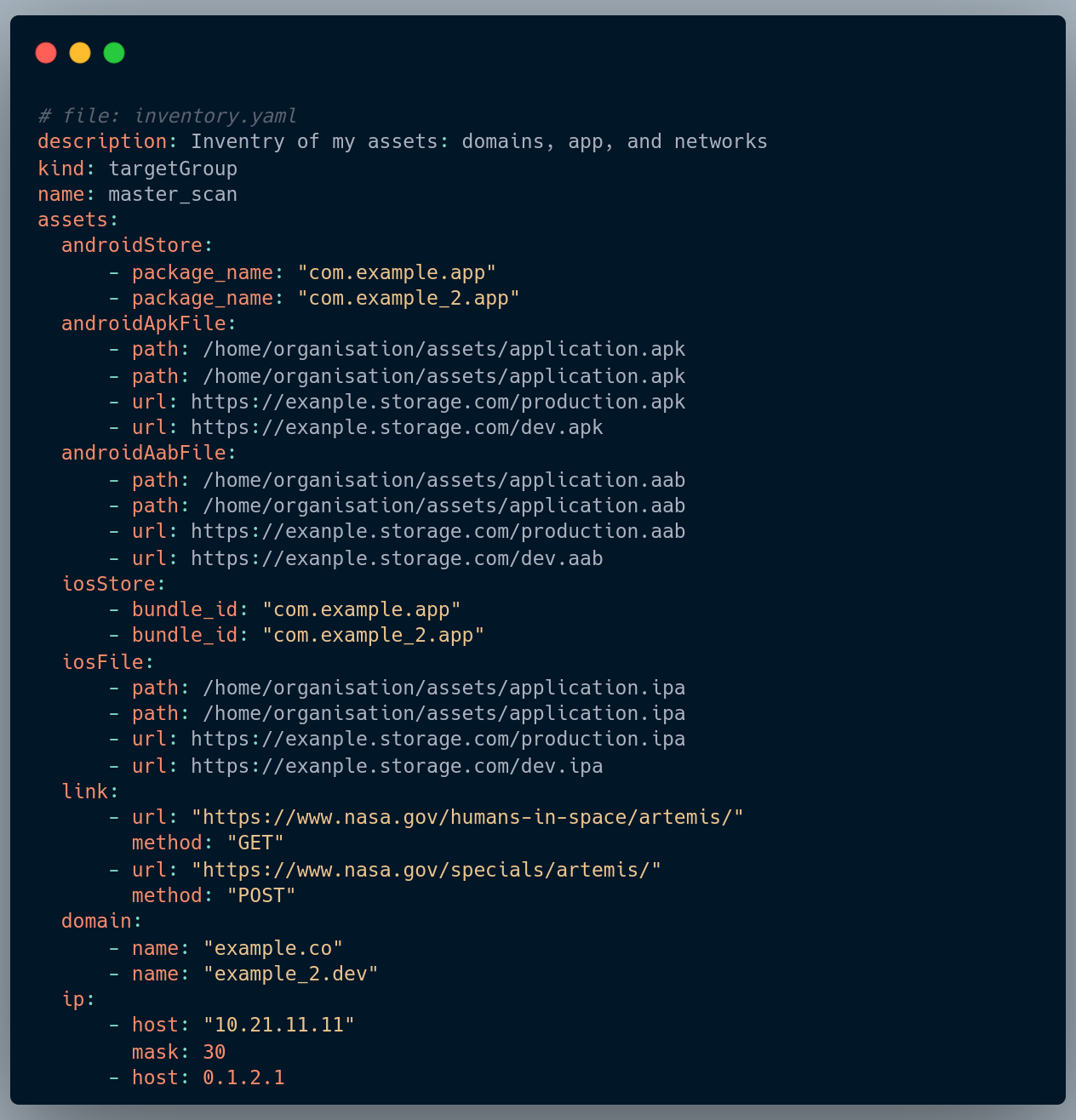
OXO is an open-source mobile security testing orchestration framework developed by our security team to automate, standardize, and scale real-world mobile application security assessments. It was built to directly address recurring operational gaps we encountered during large-scale Android and iOS pentests, where existing tools lacked workflow orchestration, repeatability, and automation across complex testing pipelines.
Our security team uses OXO as a central automation and execution layer that integrates multiple mobile security tools, enabling consistent testing, faster execution, and structured assessment workflows. By orchestrating scanning, runtime testing, and attack surface exploration, OXO allows us to reduce manual overhead, improve coverage, and operationalize mobile security testing at scale.
What It’s Best Used For
- Primary focus: Mobile security testing orchestration and workflow automation.
- Core application: Coordinating and executing Android and iOS security testing pipelines.
- Operational purpose: Standardizing assessments, reducing manual effort, and improving testing consistency.
- Testing objective: Scalable vulnerability discovery, attack surface mapping, and automated security validation.
Where It Excels
- Toolchain orchestration: Coordinates multiple mobile security tools into unified testing workflows.
- Workflow automation: Automates repetitive testing tasks, enabling faster and more consistent assessments.
- Scalable execution: Designed to support large-scale testing environments and multi-target assessments.
- CI/CD integration: Enables automated mobile security testing within development and deployment pipelines.
- Extensible architecture: Modular design allows easy integration of new scanners, testing modules, and custom logic.
- Security research enablement: Provides a flexible framework for building advanced testing pipelines and experimental workflows.
- Open source: Fully open-sourced to contribute back to the security community and encourage collaboration and transparency.
Limitations & Trade-offs
- High resource usage: Oxo scans can be memory/CPU heavy since
oxoagents are run as docker swarm services. - Customization overhead: Advanced use cases may require development of custom agents.
Typical Use Cases in Our Assessments
- Automated mobile pentesting pipelines: Orchestrating dynamic, static, and runtime testing tools.
- CI/CD mobile security validation: Continuous scanning and validation during development cycles.
- Attack surface discovery automation: Mapping endpoints, permissions, exposed APIs, and backend interactions.
- Large-scale assessment coordination: Managing testing workflows across multiple applications and environments.
- Security research and experimentation: Building custom pipelines for vulnerability research and exploit development.
7. Python
Python is a versatile programming language widely used by our security team to automate, extend, and orchestrate mobile security testing workflows. It enables rapid prototyping of custom tools, scripting of repetitive tasks, and integration between dynamic analysis, static analysis, and backend testing tools.
Our security team uses Python to build, automate, and customize testing pipelines, accelerate exploit development, interact with mobile APIs, and glue together multiple security tools into coherent workflows. Its ecosystem of libraries and frameworks allows us to move faster while maintaining reproducible, scalable, and precise security assessments.
What It’s Best Used For
- Primary focus: Automation, scripting, and custom tool development for mobile security testing.
- Core application: Developing and integrating custom scripts, scanners, and exploit tools for Android and iOS assessments.
- Operational purpose: Reducing manual effort, standardizing testing workflows, and accelerating assessments.
- Testing objective: Automating repetitive testing tasks, vulnerability discovery, and backend API validation.
Where It Excels
- Rapid scripting and prototyping: Quickly write scripts to test specific scenarios, automate payloads, or extend tools.
- Tool integration: Acts as the “glue” between Frida, OXO, and other security tools.
- Extensive library ecosystem: Leverages modules for network requests, API interaction, fuzzing, cryptography, and more.
- Custom automation pipelines: Build reusable and scalable testing workflows for mobile assessments.
- Exploit and POC development: Rapidly prototype proof-of-concept attacks and vulnerability exploits.
- Cross-platform compatibility: Works across Windows, macOS, Linux, and integrates with CI/CD environments.
- Open source: Fully supported by the Python community with extensive security-focused libraries.
Limitations & Trade-offs
- Performance limitations: Slower than compiled languages for heavy computation or large-scale fuzzing.
- Requires programming expertise: Effective use depends on scripting and automation skills.
Typical Use Cases in Our Assessments
- Automated workflow scripting: Orchestrating dynamic and static testing tools across multiple apps.
- Exploit prototyping: Developing proof-of-concept attacks for authentication, logic, or cryptography flaws.
- API testing and validation: Automated verification of backend services and endpoint security.
- Toolchain integration: Connecting Frida, OXO, and other security tools into consistent workflows.
- Security research and experimentation: Rapid development of custom scripts and testing pipelines for complex scenarios.
8. Opencode / Claude code / Gemini Code

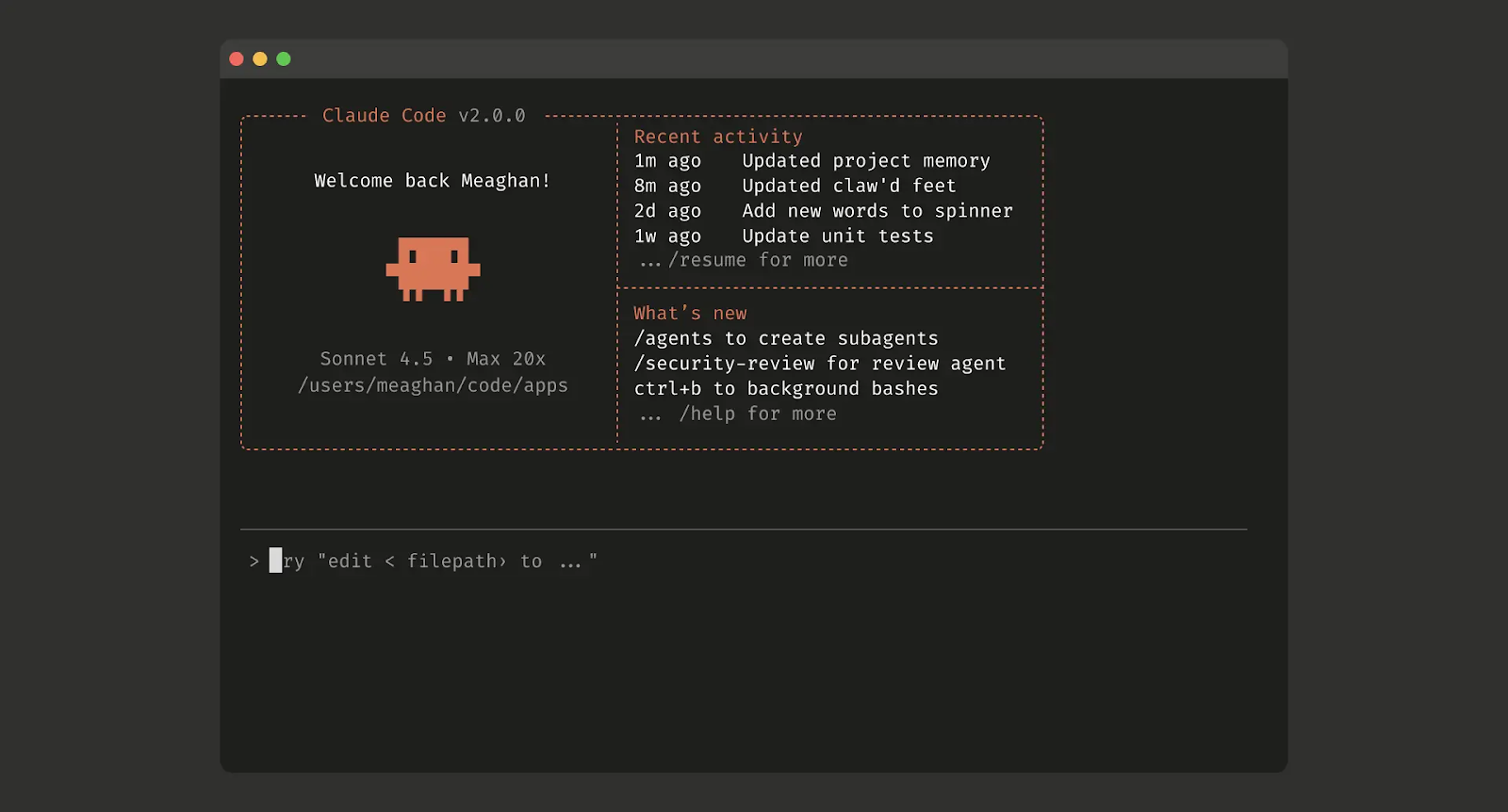
Opencode, Claude Code and Gemini Code are open-source AI-powered coding and development agents designed to assist engineers and security teams directly inside their development environments, including terminals, IDEs, and desktop clients. They support multiple large language models, integrate with existing workflows, and provide real-time assistance for code generation, debugging, refactoring, and analysis.
Our security team uses Opencode, Claude Code and Gemini Code as productivity and acceleration layers across security engineering, tooling development, exploit prototyping, automation scripting, and research workflows. They help us move faster when building custom testing utilities, writing proof-of-concept exploits, automating assessments, and performing deep technical analysis during mobile and backend security engagements.
What they’re Best Used For
- Primary focus: AI-assisted development, scripting, and technical analysis.
- Core application: Rapid development of security tooling, exploit prototypes, and automation workflows.
- Operational purpose: Accelerating security engineering tasks, research workflows, and testing automation.
- Testing objective: Speeding up script writing, payload generation, exploit validation, and tooling customization.
Where they Excels
- Code generation and assistance: Helps our team rapidly write scripts, exploits, and automation logic for security testing.
- Multi-model support: Works with multiple LLM providers and local models, enabling flexibility across environments and privacy needs.
- IDE and terminal integration: Operates directly inside development workflows, reducing context switching and friction.
- Automation and scripting acceleration: Dramatically shortens development cycles for custom tooling and security workflows.
- Privacy-first design: Does not store source code or session context, making it suitable for sensitive security projects.
- Open source and extensible: Fully open-source with active community development and extensibility.
Limitations & Trade-offs
- Model-dependent accuracy: Output quality depends heavily on the selected model and prompt quality.
- Security verification required: Generated code and logic must always be manually reviewed for correctness and security.
- Context limitations: Large or highly complex projects may require careful context management to maintain accuracy.
- Not a replacement for expertise: Acts as productivity multipliers, not substitutes for deep security engineering knowledge.
- Operational overhead: Requires careful integration into workflows to avoid dependency or complacency risks.
Typical Use Cases in Our Assessments
- Security automation scripting: Rapid development of custom testing and orchestration scripts.
- Exploit prototyping: Creating and refining proof-of-concept exploits and attack workflows.
- Payload generation: Assisting in fuzzing logic development and payload creation.
- Toolchain integration: Connecting multiple security tools into automated workflows.
- Security research support: Accelerating vulnerability analysis and reverse engineering tasks.
9. Docker / Docker Compose
Docker and Docker Compose are containerization tools that let our security team spin up isolated, reproducible testing environments. Rather than manually setting up servers, databases, or backend services for each mobile assessment, we can package everything in containers, run it anywhere, and reset it instantly when needed. This makes testing faster, more consistent, and safer, especially when dealing with complex mobile backends.
We use Docker and Docker Compose to host security tools, replicate multi-service backends, and automate environment setup, ensuring that every assessment starts from a clean, standardized state. They’re not testing tools themselves, but they make everything else work reliably and at scale.
What It’s Best Used For
- Primary focus: Containerized environment management for security testing and development.
- Core application: Running isolated testing labs, mobile backend emulators, and multi-service applications.
- Operational purpose: Standardizing environments, ensuring reproducibility, and reducing setup time.
- Testing objective: Rapid deployment of mobile and backend test environments with minimal manual configuration.
Where It Excels
- Environment consistency: Guarantees identical setups across local, cloud, and CI/CD pipelines.
- Rapid deployment: Spin up or tear down services and testing environments in seconds.
- Multi-service orchestration: Compose multiple containers for databases, APIs, and app backends.
- Isolation and safety: Prevents conflicts with local system dependencies, improving reliability.
- Integration with CI/CD: Enables automated testing pipelines for mobile and backend security assessments.
- Scalability: Supports both single-host and distributed deployments for larger testing scenarios.
Limitations & Trade-offs
- Learning curve: Requires understanding container concepts, images, volumes, and networking.
- Resource overhead: Multiple containers can consume significant CPU and memory.
- Not a testing tool itself: Needs actual security tools inside containers for analysis and assessments.
- Operational setup: Initial environment configuration and container orchestration can take planning.
- Dependency management: Misconfigured images or outdated containers can affect reliability and results.
Typical Use Cases in Our Assessments
- Portable testing labs: Quickly reproduce mobile app backend environments for testing.
- Tool hosting: Run mitmproxy, or other security tools in isolated containers.
- CI/CD integration: Automate vulnerability scanning and runtime testing in pipelines.
- Multi-service simulation: Replicate complex backend services for API and workflow testing.
- Experimentation and research: Safely test exploits or attack flows without impacting production systems.
10. Nuclei
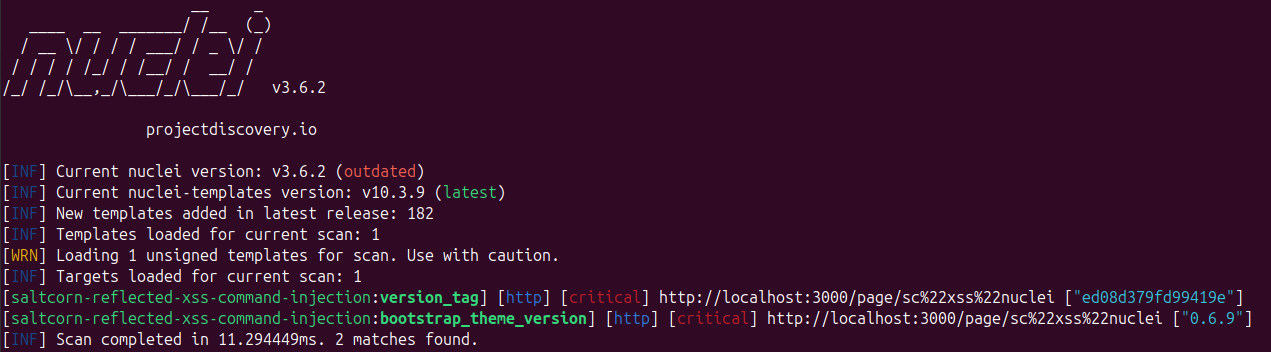
Nuclei is an open‑source, vulnerability scanner powered by a community‑driven template ecosystem and built on a simple YAML‑based DSL. It allows security teams to define custom detection logic for a wide range of vulnerabilities, simulating real‑world exploit steps with speed and accuracy.
Our security team uses Nuclei to automate and scale targeted vulnerability detection across web services, APIs, networks, and other mobile‑related infrastructure, providing rapid insight into attack surfaces and configuration issues.
What It’s Best Used For
- Primary focus: Automated vulnerability scanning using customizable templates.
- Core application: Detecting known issues, misconfigurations, CVEs, and exposed services.
- Operational purpose: Accelerating broad vulnerability discovery with minimal manual overhead.
- Testing objective: Continuous and repeatable assessment of web, API, and network attack surfaces.
Where It Excels
- Template‑driven detection: Uses simple YAML templates to define vulnerability checks, enabling quick customization.
- Community ecosystem: Thousands of templates contributed by security researchers around the world.
- Speed and scalability: Ultra‑fast parallel scanning with minimal false positives.
- Multi‑protocol support: Scans HTTP, DNS, TCP, SSL/TLS, WebSocket, and more.
- Workflow integration: Easily integrates into CI/CD pipelines and automation tooling.
- Custom templates: Create organization‑specific checks for unique attack vectors.
- Open source: MIT‑licensed and actively maintained by a large security community.
Limitations & Trade‑offs
- Template dependence: Effectiveness relies on the quality and coverage of available templates.c=
- Not a full DAST replacement: Focused on detection based on defined checks; deeper exploitation may require manual follow‑up.
- Learning curve: Writing effective custom templates takes familiarity with YAML and detection logic.
- False signal risk: Template scanning can return noisy results without filtering and context.
- Runtime only: Does not perform binary analysis or runtime hooking; best when paired with other tools.
Typical Use Cases in Our Assessments
- Reconnaissance and discovery: Fast identification of exposed endpoints, services, and common misconfigurations.
- Template‑based vulnerability detection: Scanning for CVEs, default credentials, and security misconfigurations.
- API and web scanning: Automated checks against web APIs, endpoints, and backend logic.
- CI/CD integration: Continuous security validation as part of automation pipelines.
- Custom workflow automation: Chaining templates to simulate multi‑step attack scenarios.
Bonus: Ostorlab Platform
Each of the tools we’ve covered excels at a specific part of mobile penetration testing.
Frida handles runtime instrumentation, Ghidra and JADX cover static analysis and reverse engineering, mitmproxy and Wireshark focus on network traffic, OXO and Python help automate and orchestrate workflows, and Opencode, Claude Code and Gemini Code accelerate coding, scripting, and exploit prototyping. Together, they form a complementary toolkit for thorough Android and iOS assessments.
Ostorlab unifies all these capabilities into a single platform. Our AI-driven mobile penetration testing accelerates assessments across dynamic, static, and network layers, while every finding is validated by human experts to ensure accuracy. From vulnerability discovery to attack surface mapping, CI/CD integration, and automated reporting, Ostorlab covers every stage of mobile pentesting without the need to switch between multiple tools.
For security teams aiming for speed, precision, and complete coverage in mobile penetration testing, Ostorlab provides an end-to-end solution that complements traditional tools, streamlines the entire assessment workflow, and replaces the manual orchestration of multiple solutions.
Know Your App's Weaknesses Before Attackers Do
Your mobile security toolkit is only as good as the visibility it gives you. Run a free scan to uncover vulnerabilities across your Android and iOS apps in minutes.