Mon 20 April 2026
Introduction:
Mobile game security testing matters more now than ever. Today, attackers go far beyond simple cheating. They use AI-powered cheats, automated bots, and malware to steal accounts, generate unlimited in-game currency, unlock premium items without paying, or farm rare rewards automatically.
These attacks don’t just affect individual players, they can expose personal data, ruin fair play, and can hurt both the game’s revenue and reputation. When left undetected for too long, players notice before developers do. Frustration builds, the community starts leaving, and by the time the damage is visible it is already hard to reverse.
With attacks becoming more advanced and harder to spot, simply reacting after a problem appears isn’t enough. That’s why developers turn to security testing. Security testing is essential because it looks beyond the game itself. It examines the gaming app, the network it communicates over, and the backend systems that manage player data and transactions.
Why Mobile Games Are Prime Targets for Hackers
According to Kaspersky’s Gen Z Gaming Report 2025, 19,038,175 attempted attacks used the names of popular Gen Z games to disguise malicious files between the second quarter of 2024 and the first quarter of 2025. Following the same report, mobile gaming has grown 9% since 2020, with 82% of Gen Z playing on their phones while also gaming on PC and consoles. Over half spend more than $20 per month on in-game items and subscriptions, making them a prime target for hackers.
With so many players investing time and money, mobile games naturally attract hackers looking to exploit vulnerabilities and gain an advantage. Let’s break down the main reasons hackers go after them
High Revenue and Large Player Bases are Attractive for Hackers
Mobile games with lots of players and in-app spending naturally attract hackers. Games with in-app purchases, virtual currencies, or paid content can be exploited to get currency or items without paying. The more popular a game is, the easier it is for hackers to scale their attacks. Attackers can take over thousands of accounts, farm resources automatically, or abuse reward systems across many players.
For example, games like Clash of Clans and PUBG Mobile, which have generated billions in revenue and boast hundreds of millions of monthly users, have seen widespread account takeovers where hackers use stolen credentials to siphon gems or skins for resale on black markets.
Game Design, Progression, and Frequent Updates can be Exploited
Many mobile games are designed to keep players engaged with fast rewards, progression systems, and live events. While these features make gameplay exciting, they also create opportunities for hackers.
Attackers can exploit progression mechanics to level up faster than intended, unlock premium content without paying, or gain unfair advantages in competitions. Frequent updates and live events introduce new code and features, and every update is a potential gap before security checks catch vulnerabilities. Hackers can take advantage of these windows to manipulate rewards, bypass protections, or disrupt the game economy, making even well-designed games vulnerable if security isn’t continuously enforced.
Example: “PUBG Mobile - Skins and Event Exploits”
In PUBG Mobile, players earn cosmetic items, skins, and rewards through event participation and seasonal progression. Hackers have exploited these systems by:
- Duplicating rare skins or in-game currency using modified clients or memory injection.
- Completing event challenges automatically with bots or scripts, gaining rewards faster than intended.
- Abusing live events that introduce new mechanics before security patches are fully rolled out.
Cheating remains widespread in popular games like PUBG Mobile: in just one week, from August 25 to August 31, 2025, PUBG: BATTLEGROUNDS permanently banned 170,165 accounts, 162,329 of them for cheating showing just how many players attempt to gain unfair advantages.
Mobile Games Are Easier to Tamper
Mobile games are especially vulnerable to client-side tampering. Game progression, currency, and event data is stored locally on the device before syncing with the server. This creates opportunities for attackers to modify game behavior on the client side before the server validates it.
Hackers often target rooted or jailbroken devices. They use memory editors, modified game clients, and network proxies to manipulate things like currency, health, timers, or event progress. Even simple bots or automation scripts can perform repetitive tasks faster than a human player, giving cheaters an advantage.
Because mobile games are easy to install and share, even small client-side exploits can spread quickly through player communities or black-market forums. This low barrier for tampering encourages cheating, account abuse, and fraudulent in-game economies, affecting both players and developers.
PUBG Mobile, as mentioned in the previous section, is a clear example of how fast this can scale hundreds of thousands of accounts banned in a single week, with cheat tools openly advertised across social media platforms.
Top Mobile Game Threats in 2026
Mobile games get attacked from multiple directions, and the methods keep getting more advanced. Here are the main threats mobile games are dealing with today.
AI Powered Bots and Account Takeovers
Bots are a lot more advanced thanks to AI: farming resources, completing challenges, and climbing leaderboards without raising immediate red flags. By mimicking human behavior, including timing, movement, and decision-making, they can slip past automated anti-cheat systems. Some even work in groups across multiple accounts, exploiting in-game economies or finishing large-scale events faster than any human could.
Account takeovers are another major problem. Attackers use a mix of simple tricks, like phishing or password reuse, and more advanced methods such as credential stuffing, brute-force attacks, or session hijacking on unsecured networks. Once inside, they can drain currency, grab rare items, automate progression, or sell accounts on black-market platforms, causing headaches for both players and developers.
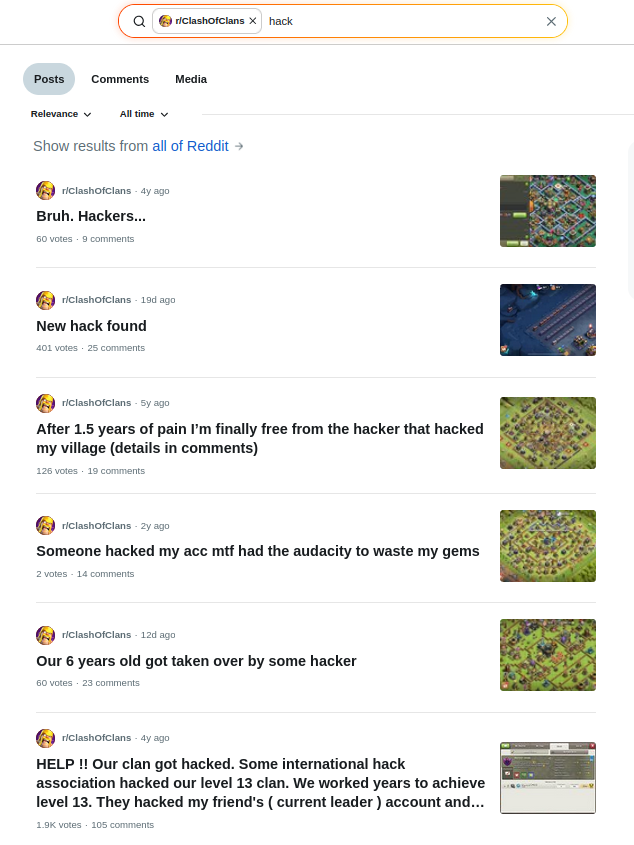
As we’ve seen in games like Clash of Clans, where multiple players on Reddit have been complaining that their account got hacked, even long-established accounts in very popular games are vulnerable to these attacks.
Tampering, Modding, and Reverse Engineering
Tampering remains one of the most common entry points. Games get modified directly on the device to manipulate currency, health, or progress before the server even sees it. Reverse engineering goes further, letting attackers decompile the game entirely and rewrite its rules, skip cooldowns, or unlock paid content for free.
A study of the top 50 games on Google Play by Denuvo reveals how common tampering and cheating are. Denuvo examined 64 cheating and cracking sites and found cheats for 86% of these games, with tampered APKs available for 84%. For 80% of the titles, cheats existed for the latest version, and memory editor hacks worked on 22%.
This shows how attackers reverse engineer mobile apps, alter the APK or memory to create cheats, and then redistribute modded versions that manipulate game logic, currency, and progress without the server noticing
Economy Damage and IP Theft (Copycats)
When a transaction bug goes unpatched, players can complete a purchase and then reverse it, ending up with both the item and their currency intact. Trade window glitches work similarly, letting players duplicate rare items by manipulating the exchange process. Over time this floods the economy and breaks the balance for everyone playing legitimately.Modded APKs carrying these exploits spread freely on third-party sites, often repackaged with malware.
Reverse engineering is what sits behind all of this, and copycats also use reverse engineering tools to extract art, maps, and gameplay mechanics straight out of the original game. They then repackage everything into a near-identical title and publish it on alternative app stores under a different name. This is IP theft, where the studio's owned creative work, the characters, visuals, and game design, gets stolen and monetized by someone else without permission.

Pocket Monster Reissue is a documented example of mobile IP theft. Chinese developers released the copycat game in 2015, copying Pokémon's character designs, gameplay mechanics, and branding almost entirely. The copycat generated $42 million in its first year, directly monetizing IP that belonged to The Pokémon Company. It was not until December 2021 that The Pokémon Company filed a lawsuit, and by 2024 they won $15 million in damages.
Understanding these threats is the first step. The sections below cover how security testing addresses them and what developers should have in place to stay ahead.
The Business Impact of Mobile Game Hacks and Cheats
A mobile game is rarely transparent when it is compromised through hacks, cheats, or account takeovers. Players start noticing something is wrong before the development team does, whether it is an economy that feels broken, accounts getting compromised, or cheaters dominating leaderboards. The frustration shows up in reviews first, then in retention numbers.
App store ratings are particularly unforgiving. A wave of one-star reviews citing hacks or unfair gameplay is hard to recover from because it directly affects organic discovery. New players see the rating before they see anything else.
If player data was involved, the stakes get higher. GDPR violations, COPPA infractions, and PCI DSS failures carry real fines, and regulators do not factor in whether the breach was intentional. The legal and compliance cost of a single incident can exceed what months of security testing would have cost.
Revenue takes the hit last but hardest. Exploited economies devalue in-game currencies, fraudulent transactions drain payment systems, and players who feel the game is unfair stop spending. Rebuilding that trust takes far longer than fixing the vulnerability that caused it.
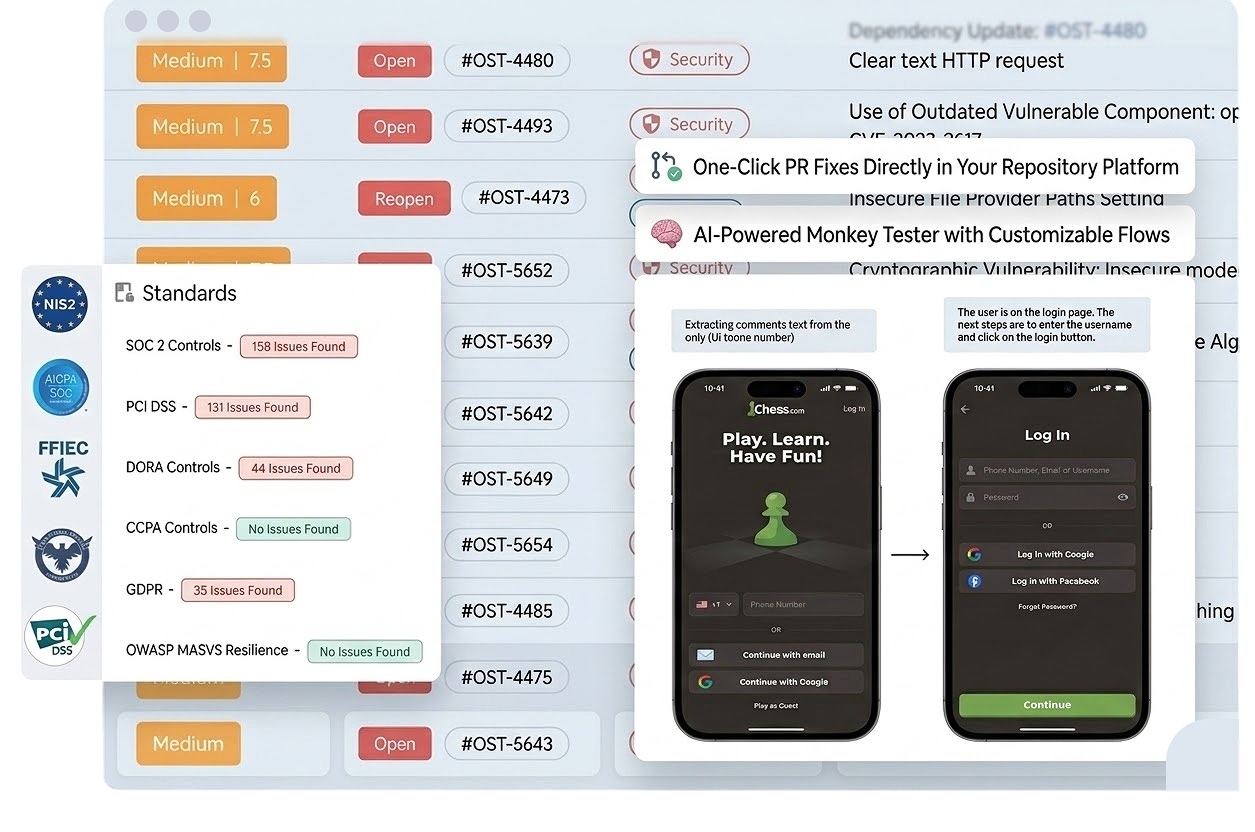
How Security Testing Protects Your Mobile Game
Mobile game security testing uses multiple layers. Each layer protects a different part of the game, from code and runtime to network, data, client integrity, and AI monitoring. The table below shows what each layer protects and how it keeps the game secure and fair.
| Security Testing Layer | What It Protects | Impact on the Mobile Game |
|---|---|---|
| Code | Game source, logic, and mechanics | Prevents players from unlocking paid content early, bypassing game rules, or modifying in-game mechanics |
| Runtime | Active monitoring while the game runs | Ensures fair gameplay by detecting cheats, hacks, abnormal behavior, and automated bot activity in real time |
| Network | Communication between game and servers | Secures multiplayer sessions, prevents score manipulation, and protects in-game transactions |
| Data | Player info and assets | Keeps player accounts, progress, and virtual currencies safe |
| Integrity | Game client on the device | Stops modded or tampered versions from giving unfair advantages or breaking the game |
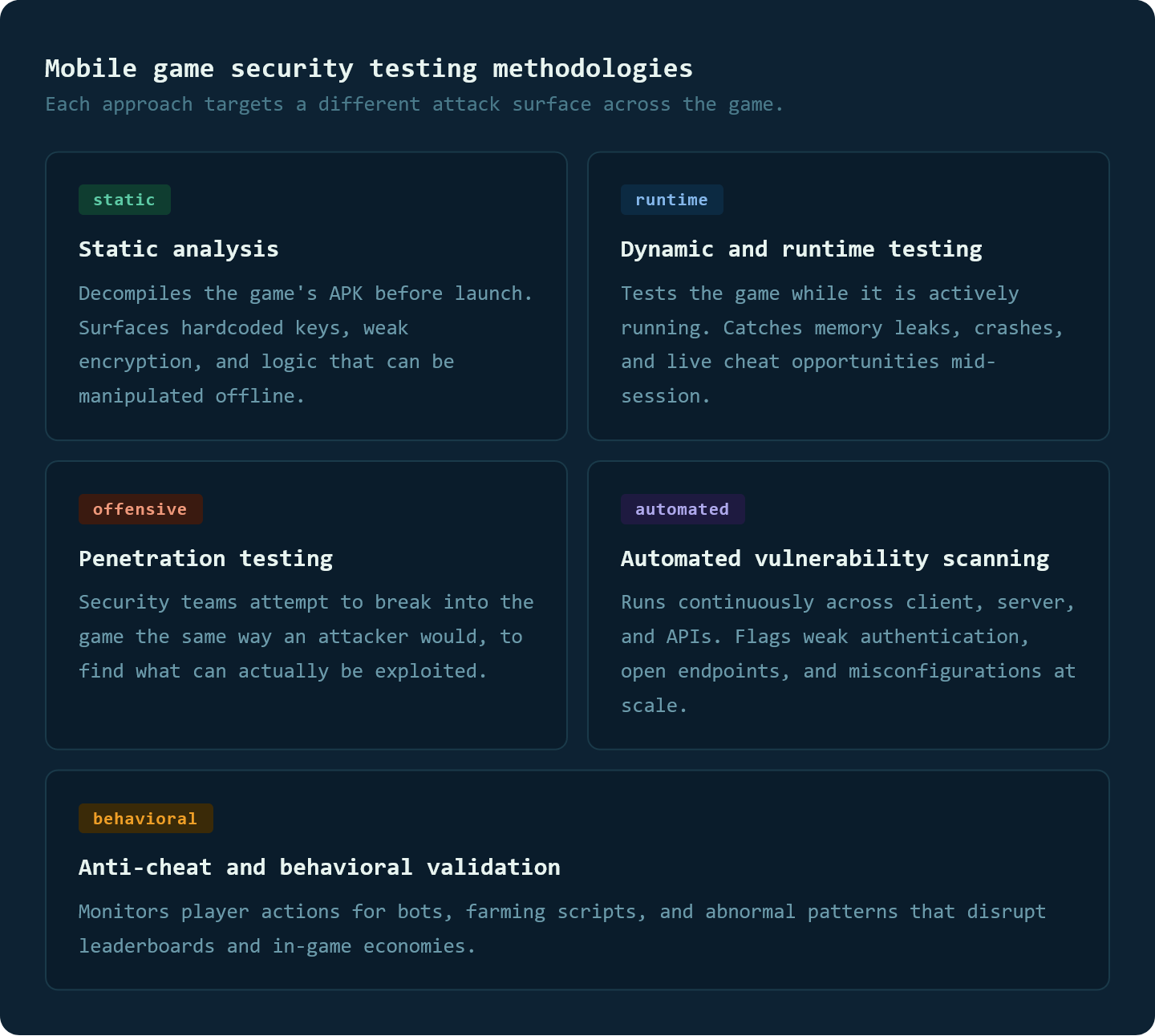
Mobile Game Security Testing Methodologies
Security testing uses different methods to find vulnerabilities, prevent cheating, and protect player data across the game. The main approaches are static analysis, dynamic and runtime testing, penetration testing, automated vulnerability scanning, and anti-cheat behavioral validation, each targeting a specific layer of the game from code to live player behavior.
How Mobile Game Security Testing Supports Compliance and Lowers Costs
Security testing not only protects players and their data but also helps ensure the game meets regulatory requirements. Detecting vulnerabilities early reduces the cost and effort of fixing issues, lowers the risk of fines, and prevents potential damage to the game’s reputation.
Relevant regulations and standards:
- GDPR – Governs the collection, storage, and processing of personal data for players in the EU, requiring consent, secure storage, and breach reporting.
- PCI DSS – Sets security requirements for handling payment information in games with in-app purchases or other financial transactions.
- COPPA – Applies to games accessible to children under 13, ensuring parental consent for data collection and protecting children’s privacy.
These standards guide how developers handle sensitive player information and secure financial operations. For mobile games specifically, the stakes are higher since a single data breach or payment exploit can trigger regulatory action and significant fines across multiple regions at once, because mobile games are played globally and different countries each enforce their own rules.
Best Practices to Secure your mobile game
Securing a mobile game requires more than a single defense. Multiple strategies work together to protect the game, its players, and revenue, while preventing cheating and exploitation. The following best practices focus on the areas that matter most.
Layered defense across client and server
A single protection point is never enough because attackers do not limit themselves to one entry. They probe the client, intercept network traffic, test the server, and look for gaps between layers. Securing the game's code, runtime environment, network communication, and backend independently means that even if one layer is bypassed, the rest continue to hold. Each layer should be treated as if the others do not exist.
Anti-cheat and economy protection
Bots and scripted exploits are not always visible right away. They accumulate over time, inflating resources, manipulating leaderboards, and making the game progressively less enjoyable for players who are not cheating. By the time the damage shows, the player base has already started leaving. Monitoring unusual action patterns, flagging abnormal transaction volumes, and validating every economy interaction server-side catches these issues before they compound.
Zero trust by default
Most security failures in mobile games happen because the server trusted what the client sent without questioning it. Zero trust flips that assumption entirely. Every player action, every transaction, and every device needs to be verified server-side before it is accepted. App attestation confirms the game has not been tampered with, integrity checks validate the client state, and continuous monitoring catches anything that slips through. The client becomes just a display layer, not a source of truth.
Following a Structured Security Testing Checklist
Mobile game security testing needs to be consistent across every release, and the approach changes depending on the platform your game runs on. Each platform has its own attack surface and vulnerabilities that need to be addressed specifically.
- Mobile app security testing checklist: covers the core security requirements across any mobile game
- Android game security testing checklist: addresses Android-specific risks including APK tampering and rooted device attacks
- iOS game security testing checklist: covers iOS-specific vulnerabilities including jailbreak detection and runtime manipulation
- Flutter game security testing checklist: tailored for cross-platform games built with Flutter
Conclusion
Mobile games are one of the most attacked platforms today, and the damage goes beyond cheating. It affects revenue, player trust, and compliance standing. Security testing is what keeps all of that in check.
The impact of a security breach does not hit all at once. Players start feeling the game is unfair, cheaters dominate, the economy feels broken, and trust erodes slowly until retention numbers make the problem impossible to ignore. Catching issues early and following the best practices of security testing is what prevents that spiral from starting in the first place.
If you want to see what is actually exposed in your game, Ostorlab's mobile game security testing covers every layer continuously, from binary to backend, as your game evolves. On top of that, Ostorlab's Mobile Agentic Deep Scan takes it a step further by actively simulating real-world attacks on your mobile game to confirm what is truly exploitable across the app, then delivers proof-grade evidence you can act on immediately.
Sources :
Reddit, r/ClashOfClans, search results for "hack", reddit.com, accessed 2026.
PUBG: BATTLEGROUNDS Weekly Bans Notice (08/25\~08/31)
Kaspersky genz gaming report 2025
Pokemon sues copycat company Pocket monster reissue for 15 million dollar
Irdeto, "Security Threats to Mobile Gaming Apps 101"
General Data Protection Regulation (GDPR)
Children's Online Privacy Protection Rule (COPPA)
Payment Card Industry Data Security Standard(PCI DSS)
Tags:
mobile game securityTable of Contents
- Introduction:
- Why Mobile Games Are Prime Targets for Hackers
- Top Mobile Game Threats in 2026
- The Business Impact of Mobile Game Hacks and Cheats
- How Security Testing Protects Your Mobile Game
- Mobile Game Security Testing Methodologies
- How Mobile Game Security Testing Supports Compliance and Lowers Costs
- Best Practices to Secure your mobile game
- Conclusion