Thu 16 April 2026
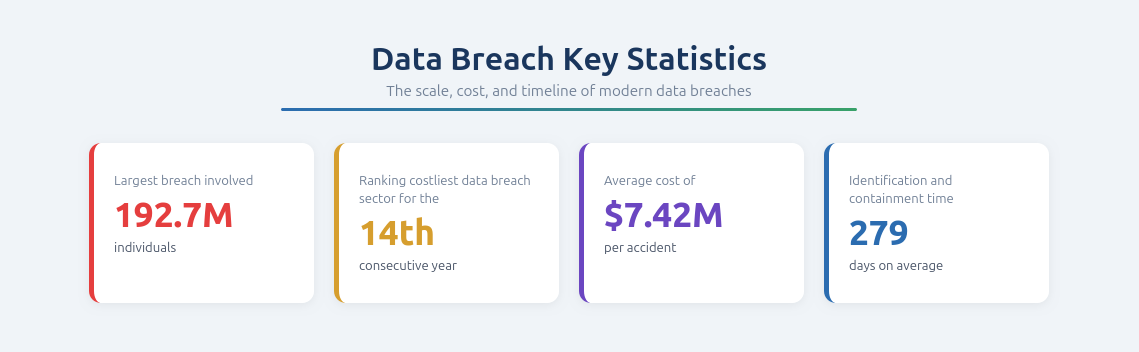
Healthcare is one of the most targeted industries today, driven by rapid adoption of digital technologies like mobile health applications, patient portals, and APIs. According to The HIPAA Journal, in 2024, healthcare breaches affected over 289 million people, a 58% increase from the previous year. The Change Healthcare ransomware attack alone impacted an estimated 192.7 million individuals, making it the largest healthcare breach in history.
As care delivery becomes application-driven, the attack surface shifts to the application layer, where sensitive data is processed and exposed. This creates intersecting risks for patient safety, sensitive data, and regulatory compliance, making application security testing essential for maintaining resilience and trust.
The Digital Transformation of Healthcare and Its Security Implications
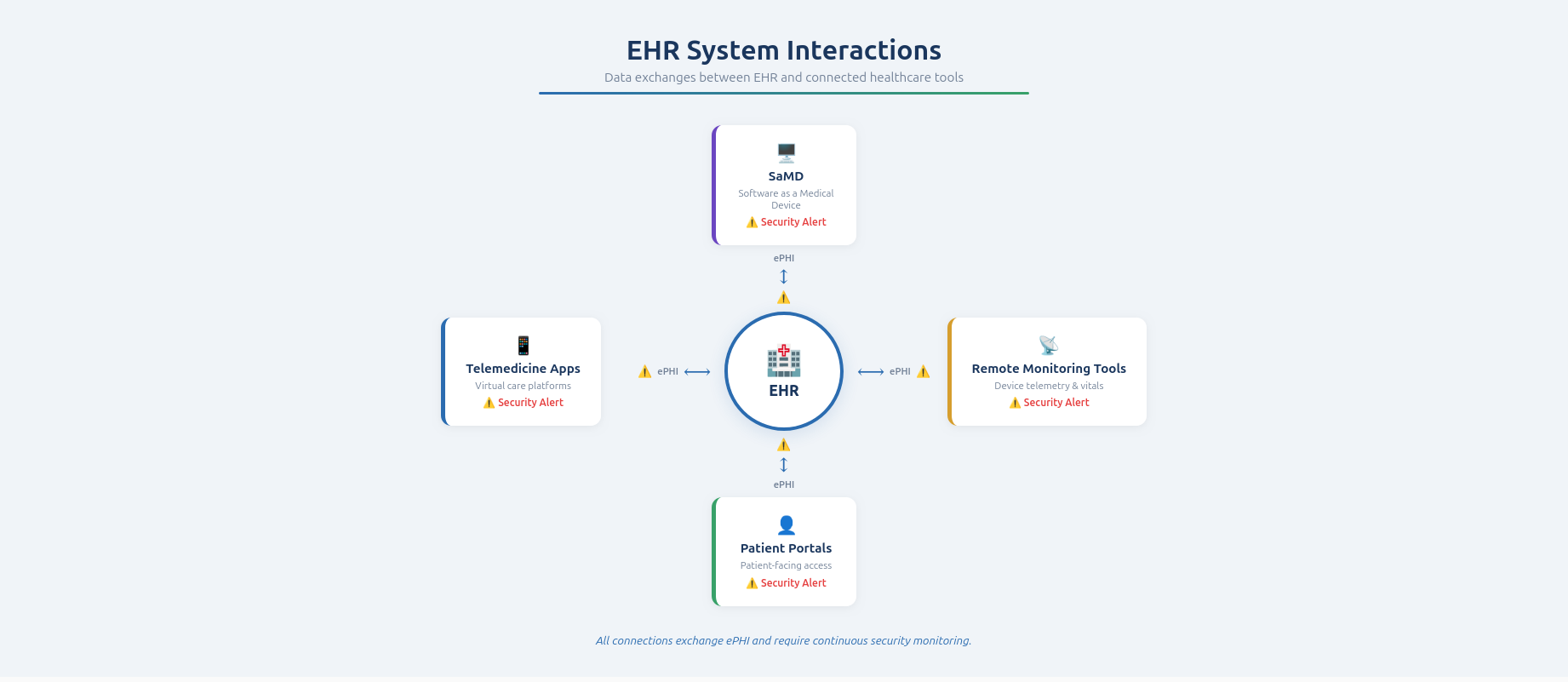
Healthcare has evolved from isolated systems into interconnected, application-driven ecosystems. Electronic Health Records now integrate with telemedicine apps, patient portals, remote monitoring tools, and cloud-native services, enabling real-time data exchange and efficient care. While this improves accessibility and operations, each integration point introduces potential security risk. The European Commission reports that healthcare experienced more cybersecurity incidents in 2023 than any other critical sector, reflecting the complexity of securing these environments.
This evolution expands the application-layer attack surface. Mobile and web apps serve as primary entry points, APIs facilitate critical data exchange, and Software as a Medical Device links software vulnerabilities to clinical outcomes. Third-party dependencies amplify risk, with over 80% of stolen health records in recent years originating from external services rather than hospitals directly.
Application sprawl further complicates security. Fragmented environments, outdated systems, and untracked APIs reduce visibility and allow vulnerabilities to persist. Continuous application security testing is vital to maintain control, identify risks early, and keep pace with modern healthcare complexity.
The Sensitive Nature of Healthcare Data
Healthcare data is uniquely valuable because it combines personal, medical, and financial information within a single record. This makes it a prime target for cybercriminals, who can exploit it for identity theft, insurance fraud, or resale on underground markets. Unlike financial data, healthcare information is difficult to change once compromised, increasing both its long-term value and the potential impact of a breach on individuals and organizations.
For the 14th consecutive year, healthcare has the most expensive data breaches of any industry, with the average cost reaching $7.42 million per incident.
IBM Security - Cost of a Data Breach 2025 Report
This sensitive data is distributed across multiple layers of modern healthcare applications. It exists in mobile and web interfaces, backend systems that process and manage workflows, APIs that enable interoperability, and connected devices that generate real-time patient data. It is often stored in cloud-based environments, further expanding the number of potential exposure points. A vulnerability in any of these components can compromise the entire data flow, making end-to-end security essential.
Electronic Protected Health Information sits at the core of these risks and must be secured across all application layers. Application security testing plays a critical role in identifying where ePHI is processed, stored, and transmitted, while validating access controls, encryption, and data handling practices. By proactively detecting vulnerabilities, organizations can prevent unauthorized access and data leakage, ensuring both regulatory compliance and patient trust.
Regulation, Compliance, and Secure Development in Healthcare Applications
Healthcare applications face strict regulations to protect patient data and system integrity. HIPAA in the U.S., GDPR in Europe, and initiatives like the EU Action Plan for hospital cybersecurity set clear requirements for data handling. Standards such as ISO/IEC 27001, HITRUST CSF, and SOC 2 define expectations around risk management, access control, and auditability. Applications are the primary interface for ePHI, making their security central to compliance, operational continuity, and patient trust.
Structured security frameworks in the development process are critical. A secure Software Development Lifecycle (SDLC) integrates security from design through deployment and maintenance, including controls, internal policies, and continuous validation. Application security testing identifies vulnerabilities early, validates mechanisms like authentication and encryption, and ensures ongoing security.
Compliance frameworks provide a structured approach to risk management and accountability. Organizations must implement controls, conduct assessments, and maintain documentation to meet standards like HITRUST, ISO 27001, or SOC 2. Application security testing delivers measurable evidence that vulnerabilities are systematically addressed, aligning practices with regulatory expectations and strengthening overall security posture.
Understanding Application-Layer Threats in Healthcare
Healthcare applications are prime targets for cyberattacks because they provide direct access to highly sensitive data and critical systems. Many of these applications are publicly accessible, from patient portals to mobile apps, which increases the likelihood of exposure. Recent statistics indicate that hacking and IT incidents now account for more than 80% of all large healthcare data breaches. At the same time, rapid development cycles and frequent updates can introduce vulnerabilities if security is not fully integrated into the development process. These factors combine to make the application layer one of the most attractive and effective points of attack for adversaries.
Common vulnerabilities in healthcare applications include insecure APIs, weak authentication mechanisms, improper handling of sensitive data, and misconfigurations. Third-party components such as external libraries, SDKs, or services further amplify risk, as any flaw in these dependencies can be inherited by the application. Exploiting these weaknesses allows attackers to access confidential information, manipulate application behavior, or gain unauthorized entry to internal systems. Addressing these vulnerabilities requires continuous, comprehensive testing and monitoring across all layers of the application ecosystem.
The consequences of application security failures in healthcare can be severe. Data breaches may expose sensitive patient information, damage organizational reputation, and incur financial and regulatory penalties. Disruptions to applications can interrupt clinical workflows, delay patient care, and compromise operational continuity. In extreme cases, attackers can leverage vulnerabilities to gain unauthorized control over critical systems, emphasizing why securing applications is essential to protecting both healthcare operations and patient safety.
Securing the Healthcare Application Ecosystem
Securing healthcare applications requires a comprehensive approach that covers patient-facing apps, APIs, software used in medical devices, and third-party integrations. Patient-facing applications, such as mobile apps and web portals, must be thoroughly tested to ensure they protect user interactions and handle sensitive data securely. This includes validating authentication processes, ensuring data is stored securely, and defending against common vulnerabilities. Because these applications are directly exposed to users, any weakness can be exploited quickly, making them a critical component of the overall security posture.
APIs play a central role in modern healthcare architectures by enabling seamless data exchange between systems, but they also introduce significant risks if not properly secured. Security testing of APIs focuses on:
- Identifying exposed endpoints
- Validating access controls and authentication
- Ensuring sensitive data is not improperly disclosed
Software as a Medical Device (SaMD) adds another layer of responsibility. These applications directly influence clinical outcomes, so vulnerabilities can have real-world implications for patient safety. Testing must ensure that SaMD is resilient, compliant, and capable of operating securely in clinical environments.
Third-party components and integrations, including external libraries, SDKs, and services, further expand the attack surface. While they accelerate development and add functionality, any vulnerability within these dependencies can compromise the broader system. Effective security strategies include continuous evaluation of these components to ensure they do not introduce hidden risks, reinforcing the integrity and security of the entire healthcare application ecosystem.
Visibility Challenges in Healthcare Application Security
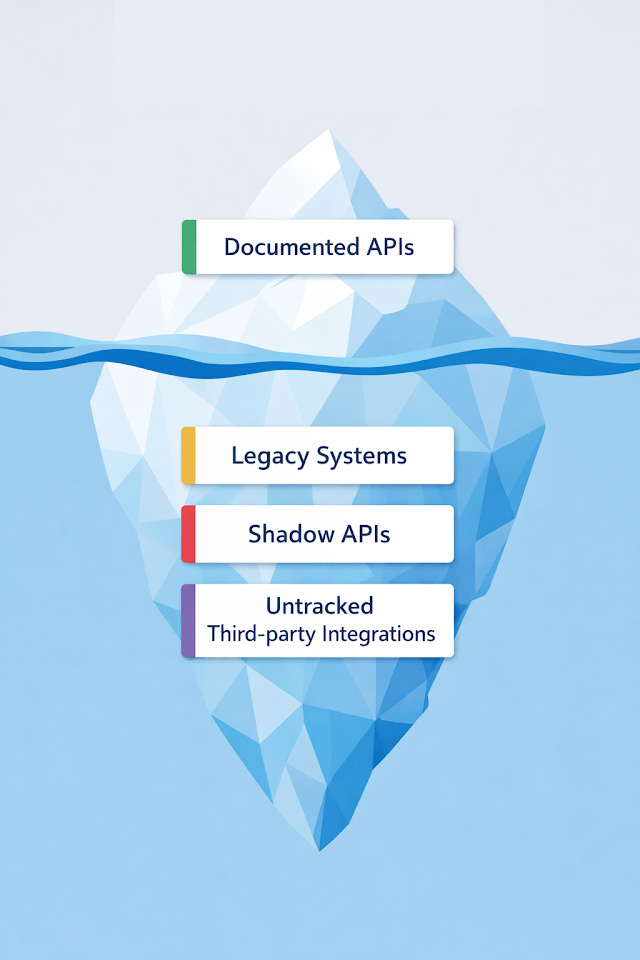
A major challenge for healthcare organizations is the lack of visibility into their application environments. Unmonitored applications, shadow APIs, and outdated systems can persist without oversight, creating hidden risks that are often overlooked during security assessments. These untracked assets become prime targets for attackers, as vulnerabilities can exist unnoticed and be exploited before detection. Maintaining clear visibility across all application components is therefore essential to reducing exposure and ensuring a strong security posture.
Healthcare environments are highly dynamic, with new applications, updates, and integrations introduced regularly. Continuous discovery is critical to maintain an accurate inventory of assets and track changes as they occur. This process ensures that all applications and APIs are included in security testing and monitored effectively. Key elements of continuous discovery include:
- Mapping all active applications and APIs across the ecosystem
- Tracking version changes and updates in real time
- Identifying previously unknown or forgotten assets
Attack surface management complements continuous discovery by providing a structured approach to assessing and monitoring exposed assets. By maintaining an up-to-date map of the application ecosystem, organizations can better understand their risk exposure, prioritize security efforts, and ensure that no critical components are overlooked. This systematic approach enhances the effectiveness of application security testing and strengthens the organization’s overall security posture.
Building a Robust Healthcare Application Security Testing Strategy
Integrating Security Testing Into the Development Lifecycle
A robust healthcare application security strategy begins with integrating testing directly into the software development lifecycle. Identifying vulnerabilities early, during design and development, dramatically reduces the risk of exposing sensitive data or disrupting critical healthcare services. By embedding security testing into CI/CD pipelines, organizations can automate recurring checks, ensuring consistent coverage across all application updates and deployments.
Key practices include:
- Early threat modeling to identify potential weaknesses in application logic and architecture
- Integration of static analysis tools to catch coding errors before deployment
- Automated testing of authentication, data handling, and encryption mechanisms within CI/CD workflows
- Regular validation of APIs and third-party dependencies to ensure compliance with security standards
This proactive approach ensures that security is not an afterthought but an integral part of application development. Organizations that adopt this methodology gain a continuous view of their risk posture and can remediate issues before they affect patients or operations, creating a culture of secure development across the team.
Continuous Application Security Testing and Monitoring
A continuous testing strategy is essential to keep pace with frequent software updates, new integrations, and evolving threat landscapes. Effective strategies combine multiple testing methods, including:
- Static Application Security Testing (SAST): Examines source code for potential vulnerabilities before deployment
- Dynamic Application Security Testing (DAST): Assesses running applications to identify runtime vulnerabilities and logic flaws
- API Testing: Evaluates the security of interfaces connecting multiple systems, ensuring that sensitive data is not exposed through improper endpoints
By layering these approaches, organizations can detect previously unseen vulnerabilities, prevent exploitation of weak points, and maintain a resilient security posture. Continuous monitoring ensures that emerging threats and newly introduced risks are identified promptly, allowing teams to respond effectively before patient data or critical systems are compromised.
| Testing Method | When it Happens | What it Finds |
|---|---|---|
| SAST | During Coding | Logic flaws, hardcoded credentials. |
| DAST | During Runtime | Authentication issues, XSS, configuration errors. |
| API Testing | During Integration | Improper data disclosure, broken authorization. |
| Agentic Scan | Continuous | Complex, multi-step vulnerabilities (AI-driven). |
Aligning Application Security With Healthcare Compliance Requirements
Healthcare application security is tightly intertwined with regulatory compliance in healthcare. Testing practices that align with frameworks such as HIPAA, GDPR, HITRUST, and ISO 27001 not only protect data but also demonstrate that organizations are actively managing risk. This alignment facilitates smoother audits, reduces regulatory penalties, and builds confidence among stakeholders.
Effective compliance-focused security testing involves:
- Mapping testing coverage to regulatory and industry-specific controls
- Generating actionable reports that demonstrate vulnerabilities are addressed systematically
- Validating that data handling, access controls, and encryption mechanisms meet compliance expectations
- Maintaining audit trails of security testing and remediation activities for accountability
A well-aligned strategy ensures that security and compliance work hand-in-hand rather than as separate silos. By continuously validating controls across applications, organizations can maintain regulatory confidence while ensuring that patients’ sensitive data remains protected.
Preparing for Application-Level Incident Detection and Response
Even with comprehensive preventive measures, breaches and application-level incidents can still occur. Healthcare organizations must be prepared to detect and respond quickly to minimize the impact on patient safety and operations. This requires a structured approach that combines continuous monitoring, incident analysis, and rapid mitigation strategies.
Essential elements include:
- Real-time monitoring of applications to identify abnormal behavior and potential exploitation attempts
- Well-defined incident response procedures that prioritize critical systems and patient-facing applications
- Rapid containment measures to prevent lateral movement within the network or further data exposure
- Post-incident analysis to identify root causes, remediate vulnerabilities, and prevent recurrence
By preparing for incidents in advance, healthcare organizations can reduce downtime, protect sensitive information, and maintain operational continuity. When implemented comprehensively, this approach reinforces trust in digital health services, ensures patient safety, and demonstrates a proactive commitment to security.
The Future of Healthcare Application Security Testing
As healthcare continues to evolve into a fully digital ecosystem, application security testing must adapt to increasing complexity and scale. Modern healthcare environments are no longer composed of a few controlled systems but of dynamic, interconnected applications built on microservices architectures, API-first designs, and multi-platform deployments. This shift significantly expands the attack surface and introduces new categories of vulnerabilities that require continuous and advanced testing approaches.
At the same time, agentic AI is transforming security testing from rigid scripts into autonomous reasoning. Unlike legacy scanning, Ostorlab’s Deep Agentic Scan functions as an autonomous security researcher, navigating complex authentication hurdles like MFA, SSO, and 2FA to reach deep business logic previously only accessible to human experts. What sets this technology apart is its ability to:
- Execute Multi-Step Attack Chains: It identifies and chains low-severity flaws to demonstrate high-impact exploits, such as bypassing identity checks or uncovering BOLA in mobile APIs.
- Provide Proof-Grade Evidence: By validating every finding in real-time, it eliminates "noise" and provides developers with verified, actionable evidence; including request logs and reproduction steps.
- Analyze Mobile-Specific Boundaries: It offers specialized depth into Android and iOS ecosystems, uncovering vulnerabilities in third-party SDKs and deep-link communications that generic tools often overlook.
Ultimately, application security in healthcare goes beyond protecting systems and data, it directly supports patient safety and trust. Vulnerabilities in healthcare applications can lead to data exposure, service disruptions, and compromised clinical operations. By adopting proactive and continuous application security testing, healthcare organizations can ensure that their digital services remain secure, reliable, and resilient in the face of evolving threats.
Table of Contents
- The Digital Transformation of Healthcare and Its Security Implications
- The Sensitive Nature of Healthcare Data
- Regulation, Compliance, and Secure Development in Healthcare Applications
- Understanding Application-Layer Threats in Healthcare
- Securing the Healthcare Application Ecosystem
- Visibility Challenges in Healthcare Application Security
- Building a Robust Healthcare Application Security Testing Strategy
- The Future of Healthcare Application Security Testing