Sun 28 October 2018
Ostorlab uses dynamic analysis to assess mobile applications and enable detection of false positive free vulnerabilities.
Dynamic analysis consists of running the application on a real Android or iOS device, monitoring application interaction with different OS components and detecting insecure or potentially unsafe behaviours.
The devices used in dynamic analysis are real hardware phones and tablets equipped with different OS versions for different architectures.
During the installation phase, iOS applications (.ipa) are resigned and instrumented before installation, Android applications are installed as is without any modifications.
Once the application is installed, the instrumentation engine is hooked in and starts to intercept a plethora of API calls to detect use vulnerable behaviour, this includes crypto API, keychain, network, filesystem, SQL etc.
A monky UI fuzzer emulates random actions and tries to increase coverage of the application, at the same time a different instance is installed on a separate device where a human operator emulates complex actions that requires multiple steps, or the interaction with third systems, like email registration validation, entering an SMS validation code etc. The goal is to increase coverage of the application code.
During the analysis step, filesystem, netowork and API calls are collected, checked passively for vulnerabilities, like use of weak encryption scheme, and also dispatched to others systems to perform active testing.
During active testing, all entry points of the applications are collected and fuzzed, this includes content providers, broadcast receivers, URI handlers etc.
Backend system are also collected during this step and scanned for vulnerabilities, including SQL injection, command injection, XSS, etc.
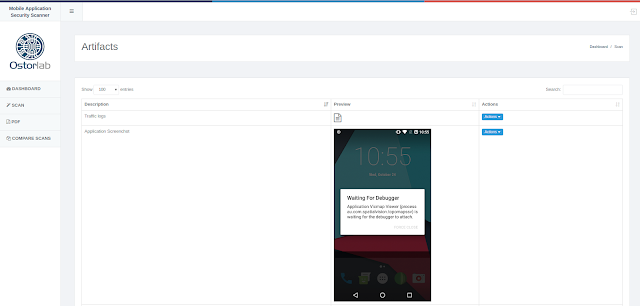
Some of the collectables are exported in the scan results as artifacts, like network log and screenshots.
Initially Ostorlab used Jailbroken and rooted devices to run all of its dynamic testing, this has proven to be unnecessary and in some cases problematic. Use of robust and fast instrumentation engines allows the collection of all the necessary information, but requires support hooking of native C level APIs, as well as platform specific APIs, like JavaScript in the case Cordova and CLI in the case of Xamarin.